bluekit.ws
https://bluekit.ws/
172.67.147.28 · Cloudflare, Inc.
Toronto, Canada
—
200 · 30.8s
Valid· E7, Let's Encrypt, US
COMPLETED
No KB/IOK detections were recorded for this scan.
bluekit.ws
Data Harvestingtechnology | finance | ecommerce | social_media | other · 4/29/2026
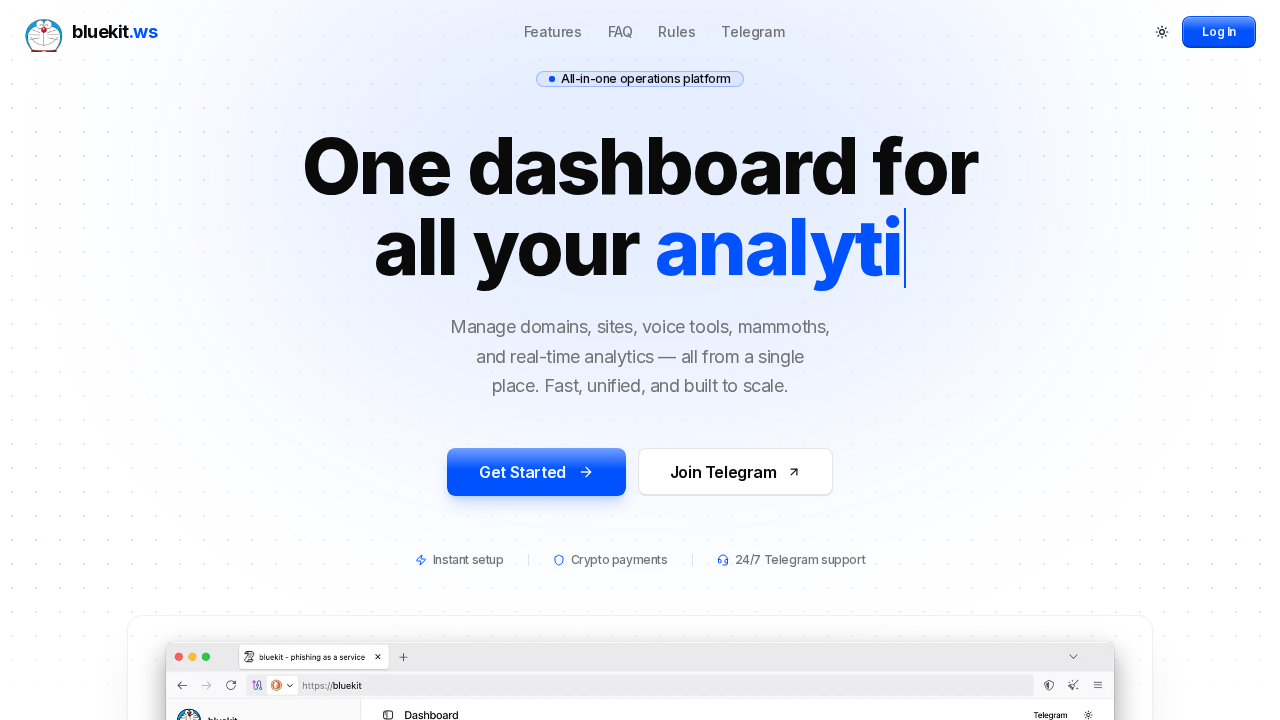
The page presents branding and UI similar to a phishing kit service called 'bluekit' and explicitly labels itself as a phishing kit in the page title. HTML title reads 'bluekit - your phishing kit' and the screenshot shows a dashboard-like UI with prominent credentials-related branding. Network and SPA-like behavior indicate credential collection potential via dynamically rendered forms, with POST activity observed to a rum endpoint and multiple external JS assets suggesting analytics/tracking and possible credential capture logic. The domain appears to be hosting a phishing toolkit rather than a legitimate service, indicating abuse potential and credential harvesting risk.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 45
Hosts: 2
Domains: 2
The site bluekit.ws presents itself as a 'phishing kit' and appears to be a tool for building or deploying phishing campaigns. The presence of SPA JavaScript bundles, dynamic credential UI, and an explicit branding around 'phishing kit' strongly suggests misuse potential and credential harvesting capabilities. Although the domain is secured behind Cloudflare and has a fresh Let's Encrypt certificate, these factors, combined with the UI messaging and observed POST beacon behavior, indicate high risk. Action is warranted to monitor and potentially take down if abuse is confirmed, given the explicit nature of the kit and the potential for credential theft.
Suspend Domain