anonflare.com
https://anonflare.com/en/sites
104.21.54.234 · Cloudflare, Inc.
Toronto, Canada
309 days
200 · 18.1s
Valid· WE1, Google Trust Services, US
COMPLETED
Domain Intelligence: anonflare.com
Scanned 3 times since Mar 17, 2026, 10:46 AM UTC
No KB/IOK detections were recorded for this scan.
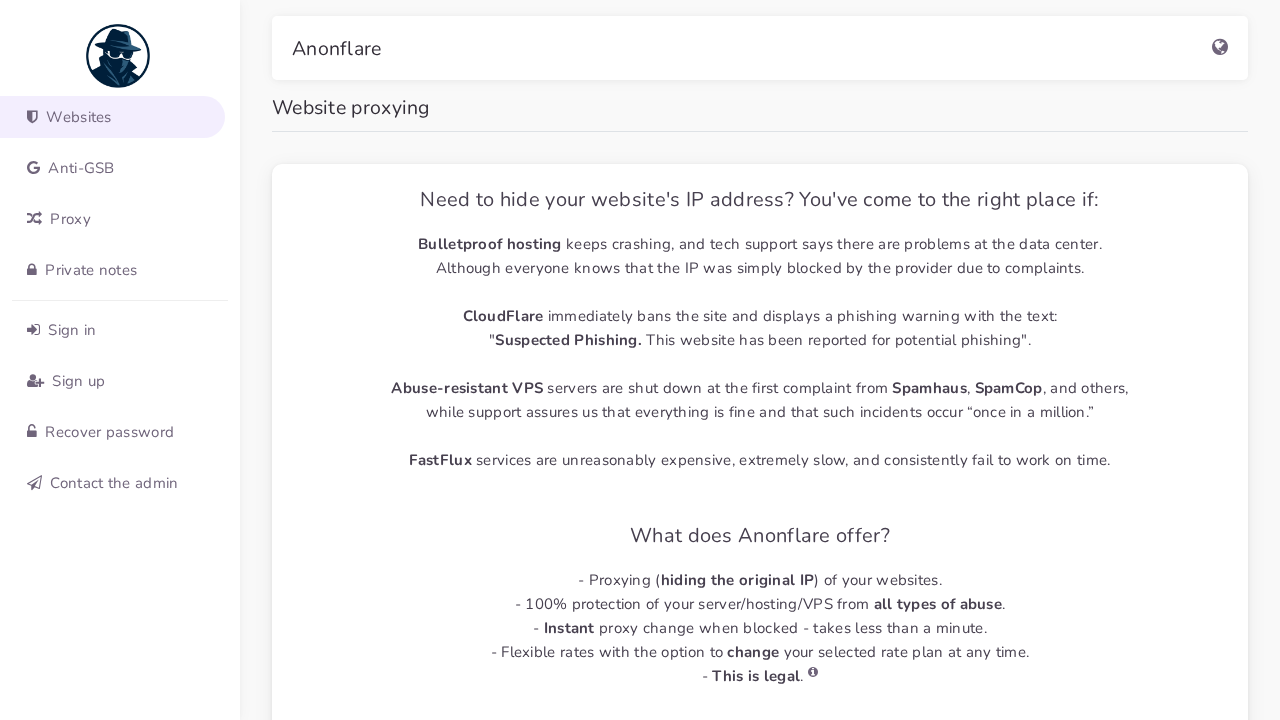
Anonflare
Unknowntechnology | other · 4/5/2026
The page presents branding for Anonflare with a dedicated sidebar and navigation, including a title 'Anonflare' and menu items under websites, proxy, and login. However, the content and imagery strongly focus on website proxying services, which is an abuse/service facilitating masking hosting/IP exposure. The domain anonflare.com is registered recently (created 2025-05-19) and uses Cloudflare, with a high number of external scripts. The page appears to be a legitimate Anonflare-like dashboard rather than a classic credential phishing page, but the presence of a proxying service raises potential abuse context. There is no direct evidence of credential harvesting on this page itself (no login form in static HTML), but dynamic SPA behavior could host credential collection. The risk signals and the visual branding strongly indicate impersonation risk only if the domain is used to deceive users about hosting/IP visibility; based on the evidence, treat as potential first-party service with notable abuse potential in proxy domain context.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 52
Hosts: 4
Domains: 4
The site presents Anonflare-branded content and appears to be a legitimate service page for proxying websites, but the real abuse risk arises from the service category (proxy/VPN-like offerings) which can be used for wrongdoing such as obfuscating hosting or IPs. The scan shows SPA-style asset loading and a POST to a CDN-rum endpoint, plus a recent domain with Cloudflare protection; these factors together indicate potential for misuse in facilitating unauthorized website proxying. Given the evidence, classify as first-party service with notable abuse potential in the proxy domain, and monitor for credential collection UI if rendered dynamically. Do not claim credential harvesting without direct evidence of a login form in the runtime UI.
Monitor