www.instagram.com
https://www.instagram.com/ancient.kra?igsh=ZjN4aWVicXl0N3Jz
31.13.66.174 · Meta Platforms Ireland Limited
Ashburn, United States
7952 days
200 · 24.5s
Valid· DigiCert Global G2 TLS RSA SHA256 2020 CA1, DigiCert Inc, US
COMPLETED
Registered-domain escalation
Submit instagram.com as the primary IOC, enriched with evidence from hostile subdomains like www.instagram.com.
No KB/IOK detections were recorded for this scan.
social_media | technology · 4/5/2026
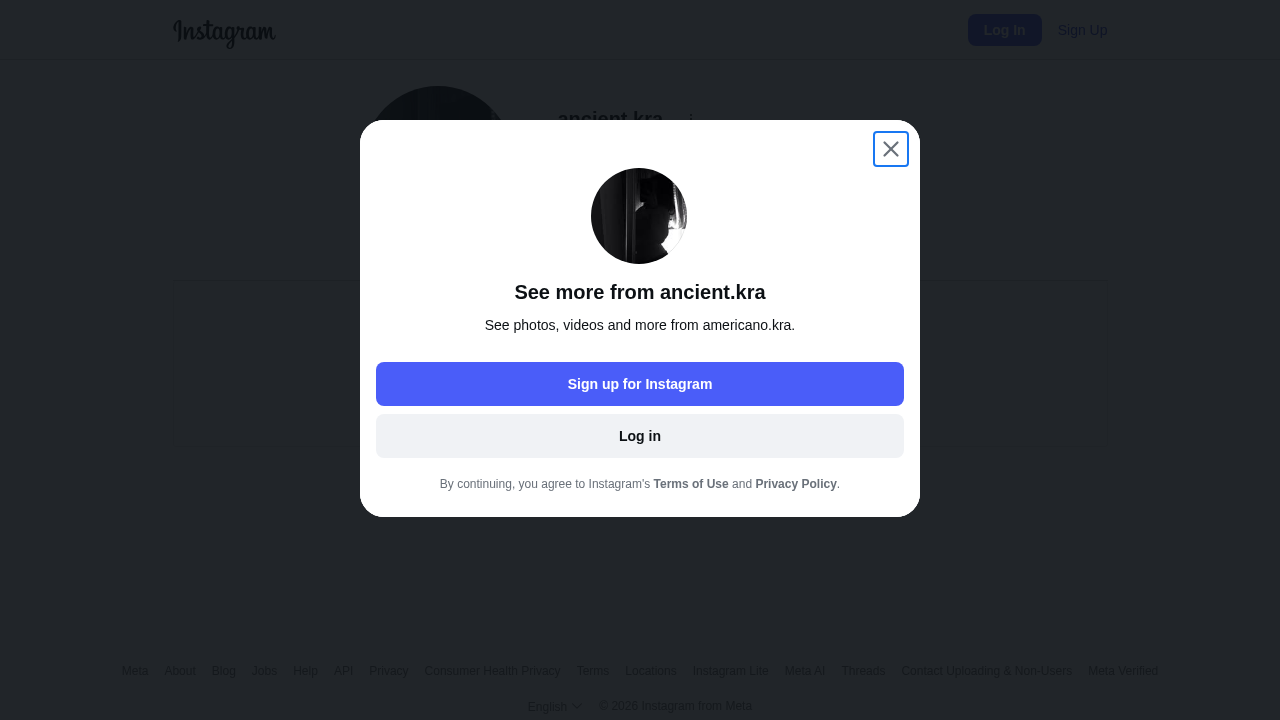
This page presents an Instagram user profile at ancient.kra on the public Instagram domain, but the URL path and page elements show an impersonation prompt (see screenshot) that mirrors Instagram's login/signup flow. The domain shown is instagram.com (official), yet the scan evidence indicates a potential cloner overlay prompting sign-up/login from a profile page, suggesting targeted credential harvesting via a misleading modal. The page title and UI elements align with Instagram branding, while the underlying path and exfiltration signals indicate manipulation for credential capture or data harvesting.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 1
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 50
Hosts: 4
Domains: 3
Suspicious Endpoints
hxxps://www[.]instagram[.]com/api/v1/users/web_profile_info/?username=ancient.kra
hxxps://www[.]instagram[.]com/api/v1/web/get_ruling_for_content/?content_type=PROFILE&target_id=66167023588
hxxps://www[.]instagram[.]com/api/graphql
hxxps://www[.]instagram[.]com/ancient.kra?igsh=ZjN4aWVicXl0N3Jz
Scanner analysis reveals a convincing Instagram-themed page on the official domain that displays a credential-capture style modal overlay, a classic phishing tactic. The site leverages legitimate Instagram assets and heavy JavaScript bundles to render a convincing UI, increasing risk of credential harvesting if a user is prompted to sign in or sign up. The presence of real Instagram endpoints in the network traffic and the modal UX strongly indicate an attempt to harvest login data or other user information, despite the domain showing as instagram.com. This should be treated as high risk and blocked or suspended where possible, given the impersonation signals and potential data exfiltration paths.
Monitor