jagex-forums.com-uk.workers.dev
https://jagex-forums.com-uk.workers.dev/portal/assisted-login-login-challenge-dc197744c4a04124a6d04da6b85adcb4-238398720-1406457486-1694086910-1863512970-169408678563454200-2-238398720-140645748/
104.21.93.83 · Cloudflare, Inc.
Toronto, Canada
2586 days
200 · 17.2s
Valid· E8, Let's Encrypt, US
COMPLETED
Domain Intelligence: workers.dev
Scanned 3 times since Mar 10, 2026, 03:40 AM UTC
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
Jagex
Vendors
29/30
Status
partial
Registered-domain escalation suggested
Suggested nowSubmit workers.dev as the primary IOC, enriched with evidence from hostile subdomains like jagex-forums.com-uk.workers.dev.
2 hostile subdomains across 3 completed scans were observed under this registered domain. Recent hosts: osrsforums.com-assisted-login-login-challenge-dc197744c4a04124a6d04da6b85a.workers.dev, jagex-forums.com-uk.workers.dev.
jagex-clone-kit
jagex-clone-kit
Directives: skipAi, skipUnblocker, skipMobileVariant
Jagex
Credential Phishinggaming | technology | education | other · 4/5/2026
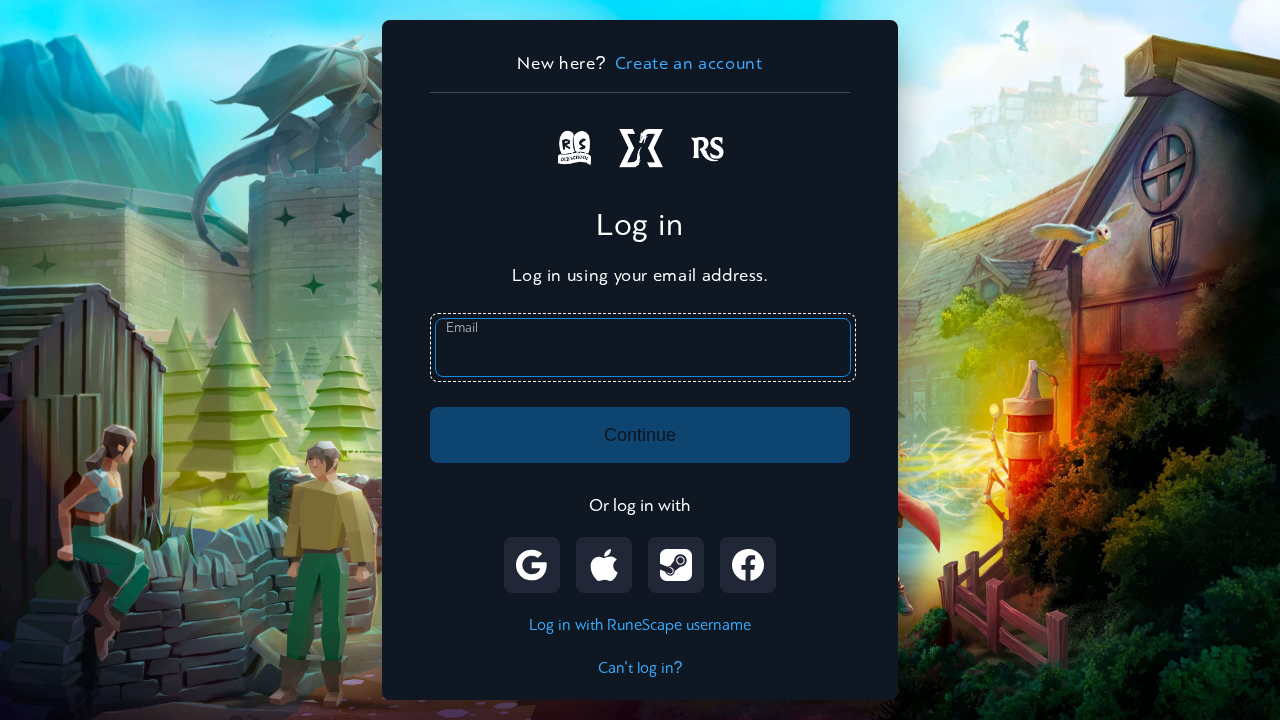
This page presents a login interface that visually imitates Jagex, but the domain is account.osrforum.it, which is not the official Jagex domain. The page title reads 'Choose how to log in | Jagex' and the UI mimics Jagex's look (logo, fonts, and layout), including a login form and social login options, suggesting credential collection. The domain impersonation, SPA-like structure, and external script loading indicate a clone designed to harvest user credentials.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 1
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 16
Hosts: 4
Domains: 4
Suspicious Endpoints
hxxps://jagex-forums[.]com-uk[.]workers[.]dev/portal/assisted-login-login-challenge-dc197744c4a04124a6d04da6b85adcb4-238398720-1406457486-1694086910-1863512970-169408678563454200-2-238398720-140645748/index.php
Scanner evidence shows a phishing clone hosting under account.osrforum.it with a page title and UI strongly mimicking Jagex. The domain does not belong to Jagex, while assets and logos are loaded from the same impersonating domain, including image and JS assets that mirror Jagex branding. The presence of a login form configured to post to a suspicious index.php and a honeypot field indicates credential harvesting behavior. The SSL certificate is newly issued for a domain attempting to impersonate a well-known brand, and the page uses a Cloudflare IP, suggesting hosting behind a WAF but not legitimate ownership. This is a high-risk credential-phishing setup intended to deceive users into entering credentials for Jagex on a non-official domain.
Monitor