storm-client.net
https://storm-client.net/
172.66.149.243 · Cloudflare, Inc.
Toronto, Canada
1242 days
200 · 16.3s
Valid· GlobalSign GCC R3 DV TLS CA 2020, GlobalSign nv-sa, BE
COMPLETED
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
Storm Store (storm-client.net)
Vendors
29/30
Status
partial
storm-store-clone-kit
storm-store-clone-kit
Directives: skipAi, skipUnblocker, skipMobileVariant
Storm Store (storm-client.net)
UnknownTechnology · 4/29/2026
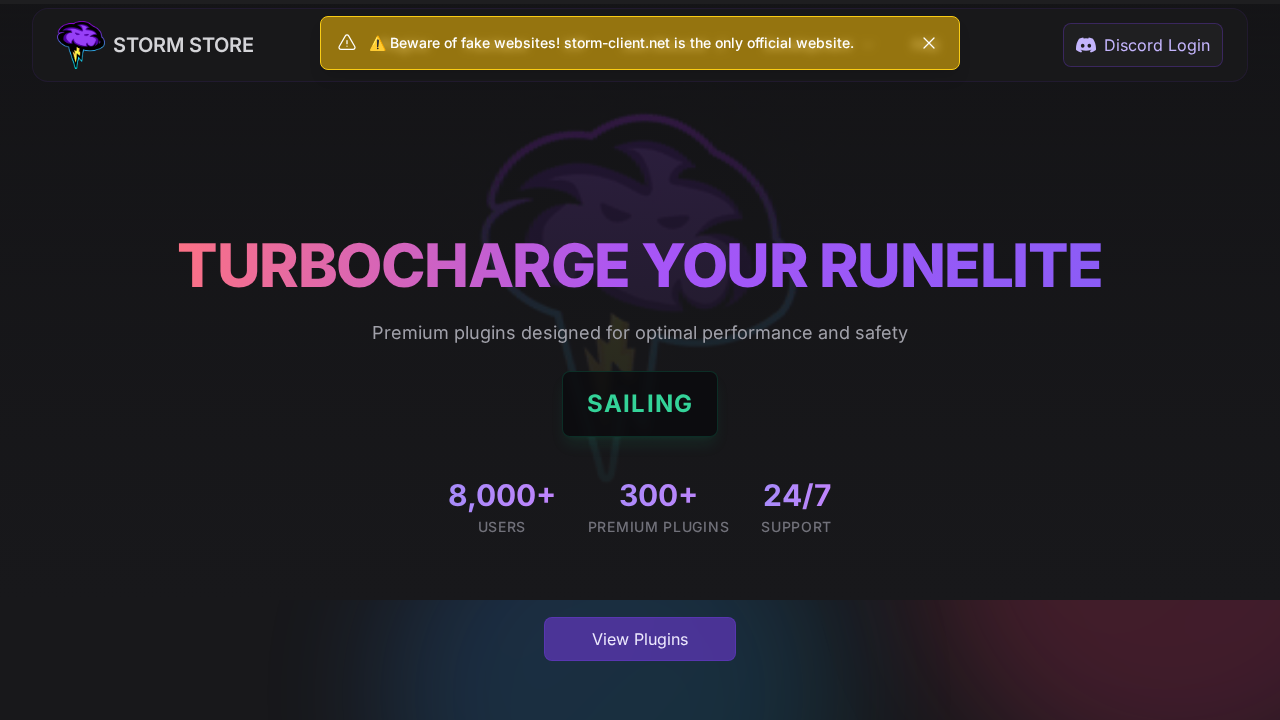
The page presents Storm Store branding with a site title and navigation that resemble a legitimate plugin store. The screenshot shows a warning bar stating “Beware of fake websites! storm-client.net is the only official website,” which is itself unusual for a first-party site. Network evidence and static HTML indicate a SPA likely collecting data via dynamic UI, but there is no explicit credential form in the static HTML. The domain uses Cloudflare and has valid SSL; the page content correlates with Storm’s branding, though the attached screenshot reveals a strong impersonation risk if the brand is being cloned for phishing on a non-official domain. Based on the evidence, the page is more suggestive of a legitimate Storm Store landing page with potential impersonation risk depending on user perception, but there is no concrete credential harvesting observed in the static data provided.
Capture
Stages: 2
Canonical: Settled Render
Changed: No
Credential Signals
Forms: 0
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 12
Hosts: 5
Domains: 5
No suspicious indicators identified
The scan identifies Storm Store branding and a page that appears to be a product landing site (Storm Store) with SPA characteristics. The presence of a prominent warning banner about the official site raises impersonation concerns, but there is no direct evidence in the data provided of credential collection or malware delivery. The domain is age-stable and uses a legitimate CDN/WAF provider (Cloudflare) with a valid SSL cert. Given the visual impersonation risk and the use of SPA that could host credential capture within JavaScript, this warrants closer monitoring and potential verification of official ownership, but the current data does not conclusively demonstrate phishing. Recommend continued observation and verification of the domain’s ownership and branding alignment with Storm’s official assets.
Monitor