bossnet.az
https://bossnet.az/portal/medieval-competitors-voting-authentication-v5a4v1d9q7q1i9n4i9y1xxs
185.32.47.214 · Bossnet LLC
Baku, Azerbaijan
—
200 · 24.1s
Valid· R13, Let's Encrypt, US
COMPLETED
Domain Intelligence: bossnet.az
Scanned 4 times since Mar 9, 2026, 12:41 PM UTC
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
Jagex
Vendors
30/30
Status
completed
jagex-login-clone-kit
jagex-login-clone-kit
Directives: skipAi, skipUnblocker, skipMobileVariant
Jagex
Credential Phishinggaming | technology | ecommerce | other · 4/5/2026
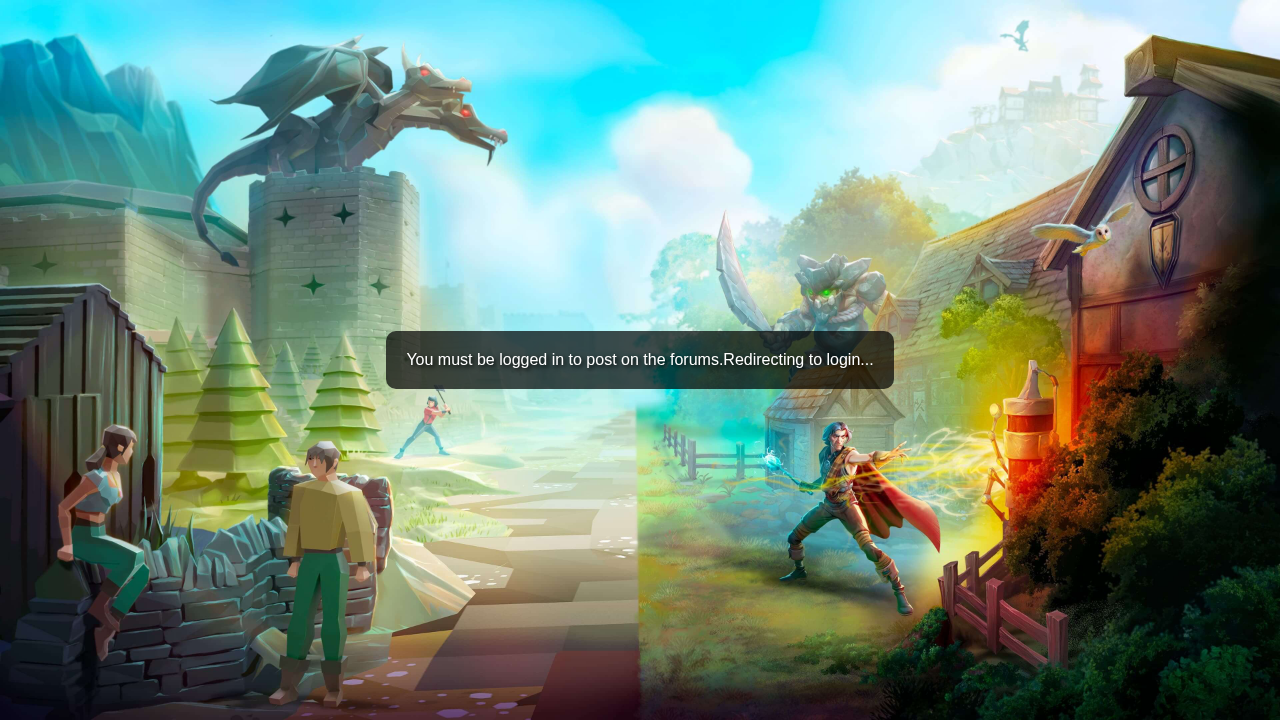
This page appears to impersonate Jagex (title 'Choose how to log in | Jagex') but is hosted on bossnet.az. The SPA-like HTML contains multiple credential-related validation scripts and a redirecting login flow, with static HTML lacking a form but JavaScript likely rendering inputs at runtime. The domain does not match the known brand domain (jagex.com), indicating brand impersonation and credential harvesting potential. The SSL cert is valid but issued by Let’s Encrypt, and the domain age is unknown; the site also loads multiple external assets and suspicious path hints in the URL.
The page presents a high risk phishing scenario: domain bossnet.az is impersonating a recognized brand by displaying a login-redirect flow labeled as Jagex. The static HTML contains no login form, but multiple JavaScript blocks suggest dynamic credential capture. Visual cues from the screenshot indicate generic game branding rather than Jagex branding, but the page title explicitly references Jagex, which is a strong impersonation signal. The site employs a valid TLS certificate from Let’s Encrypt and uses an SPA pattern, which aligns with common credential harvesting setups. The absence of WHOIS data and unknown domain age increase risk in abuse investigations. This should be treated as credential_phishing with high priority for takedown and hosting suspension.
Suspend Domain