sereneosa.com
https://sereneosa.com/
104.21.74.240 · Cloudflare, Inc.
Toronto, Canada
212 days
200 · 122.8s
Valid· WE1, Google Trust Services, US
COMPLETED
No KB/IOK detections were recorded for this scan.
technology · 4/29/2026
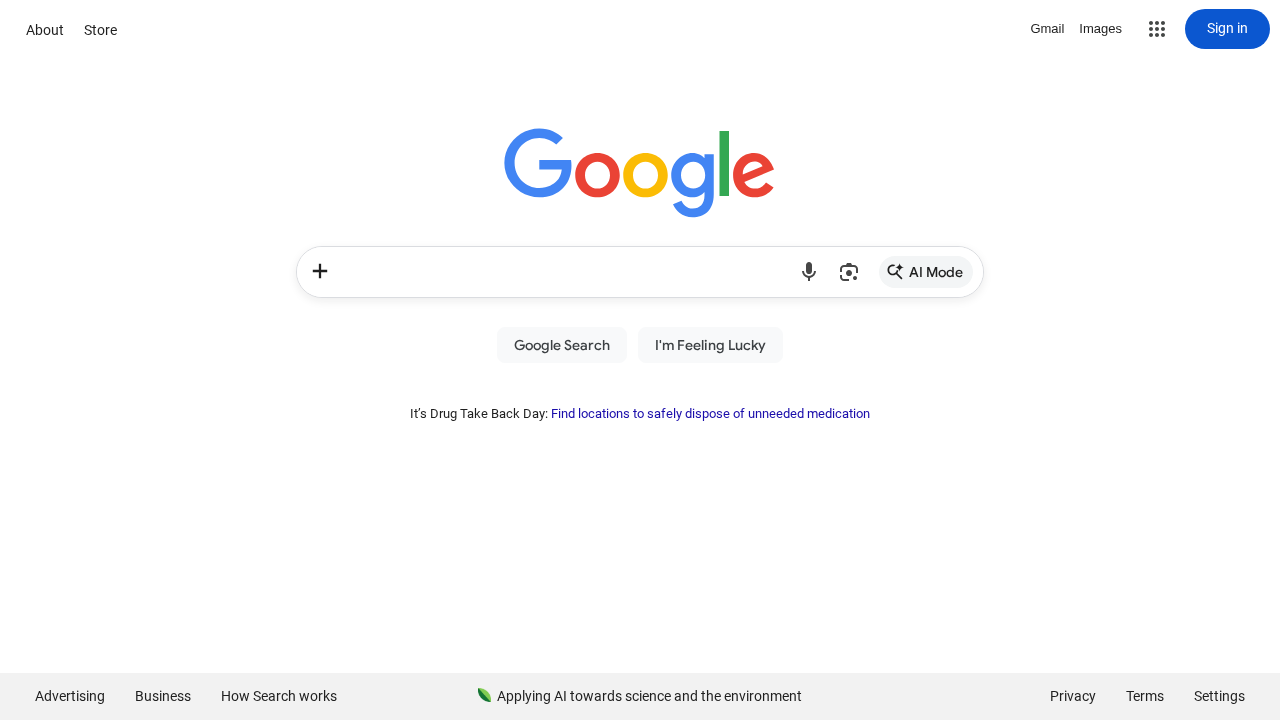
The page on sereneosa.com displays a Google branding with the Google logo, page title, and a UI surface resembling Google's search page. The final URL redirects to google.com, and the HTML shows explicit Google assets (fonts, scripts, and gen_204 endpoints) being loaded. This suggests impersonation (a typosquatted domain presenting Google branding) aiming to capture credentials or user interactions under Google’s guise, despite the domain not being an official Google domain. The presence of off-domain API calls and the final redirect to google.com further supports a phishing impersonation scenario rather than legitimate first-party content.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 1
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 56
Hosts: 9
Domains: 5
Suspicious Endpoints
hxxps://sereneosa[.]com/homeapi/collect?store_id=115864
hxxps://www[.]google[.]com/search
Off-Domain Posts
hxxps://sereneosa[.]com/homeapi/collect?store_id=115864
The scan indicates a high probability of impersonation phishing: the domain sereneosa.com presents Google branding (title, logo in screenshot, and assets) but is not the official Google domain. The page redirects to google.com, loads Google resources, and performs a POST to a non-Google endpoint (homeapi/collect) on the suspicious domain, which is a classic pattern for credential theft or data harvesting via impersonation. This warrants treating the domain as a malicious impersonation attempt and taking action to prevent victims from interacting with it. Monitor and consider blocking the URL, given the clear impersonation signals and abuse potential.
Suspend Domain