controls.gamingvote.com
https://controls.gamingvote.com/
104.21.90.15 · Cloudflare, Inc.
Toronto, Canada
4 days ⚠
200 · 19.0s
Valid· WE1, Google Trust Services, US
COMPLETED
Domain Intelligence: gamingvote.com
Scanned 13 times since Mar 10, 2026, 11:26 AM UTC
Registered-domain escalation suggested
Suggested nowSubmit gamingvote.com as the primary IOC, enriched with evidence from hostile subdomains like controls.gamingvote.com.
4 hostile subdomains across 13 completed scans were observed under this registered domain. Recent hosts: osrsjagex.gamingvote.com, rsoldschools.gamingvote.com, rsoldschool.gamingvote.com, osrsaccount.gamingvote.com.
No KB/IOK detections were recorded for this scan.
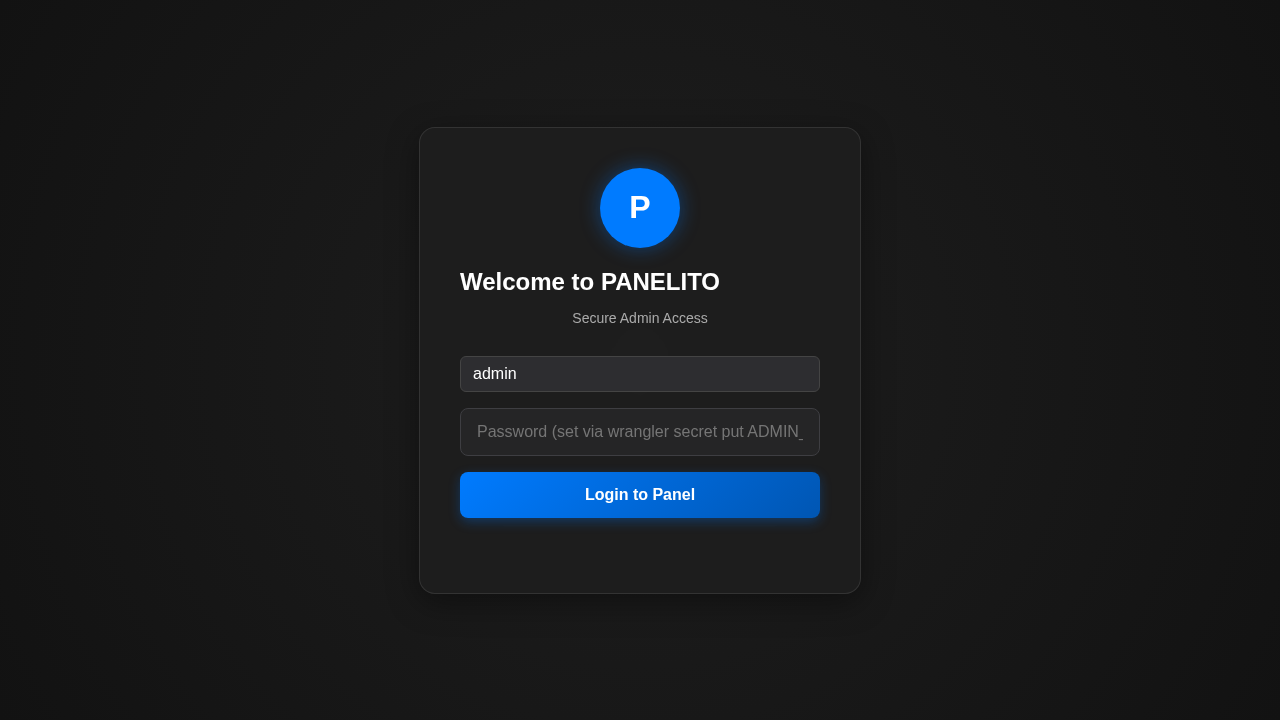
PANELITO
Credential Phishingtechnology | finance | ecommerce · 4/5/2026
The page at controls.gamingvote.com presents a LOGIN UI titled PANELITO Admin, with a password field and a single sign-in flow. The domain does not match PANELITO’s branding; visual impersonation is evident from the page title, UI copy, and logo-like circular badge. The static HTML shows a minimal shell, while dynamic JS bundles (admin.js) render a credential capture form, indicating a SPA credential harvesting setup. SSL is valid but on a very new domain (4 days old), increasing risk. External assets and off-domain endpoints hint at exfiltration behavior and third-party beaconing.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 1
Late-stage login UI: No
Resource Signals
Resources: 9
Hosts: 3
Domains: 3
Suspicious Endpoints
hxxps://usb[.]b63ccd22db3b4e5a4c4d[.]workers[.]dev/datasound/discord.mp3
Off-Domain Posts
hxxps://usb[.]b63ccd22db3b4e5a4c4d[.]workers[.]dev/datasound/discord.mp3
Abuse teams should treat this as a credential phishing site. The domain is brand-impersonating, showing PANELITO Admin branding on a page titled accordingly, with a password field and dynamic login UI rendered by JS in an SPA. The static HTML contains no forms, yet the JavaScript bundles (admin.js) render a credential collection interface, indicating intentional credential harvesting. The domain is extremely new (4 days), and the SSL cert is recently issued, both elevating risk. Off-domain exfiltration and beaconing endpoints further corroborate malicious intent. Immediate action is recommended to suspend the domain and block hosting to prevent victims from interacting with this impersonation site.
Suspend Domain