control.gamingvote.com
https://control.gamingvote.com/
172.67.193.80 · Cloudflare, Inc.
Toronto, Canada
0 days ⚠
200 · 18.3s
Valid· WE1, Google Trust Services, US
COMPLETED
Domain Intelligence: gamingvote.com
Scanned 13 times since Mar 10, 2026, 11:26 AM UTC
Registered-domain escalation suggested
Suggested nowSubmit gamingvote.com as the primary IOC, enriched with evidence from hostile subdomains like control.gamingvote.com.
4 hostile subdomains across 13 completed scans were observed under this registered domain. Recent hosts: osrsjagex.gamingvote.com, rsoldschools.gamingvote.com, rsoldschool.gamingvote.com, osrsaccount.gamingvote.com.
No KB/IOK detections were recorded for this scan.
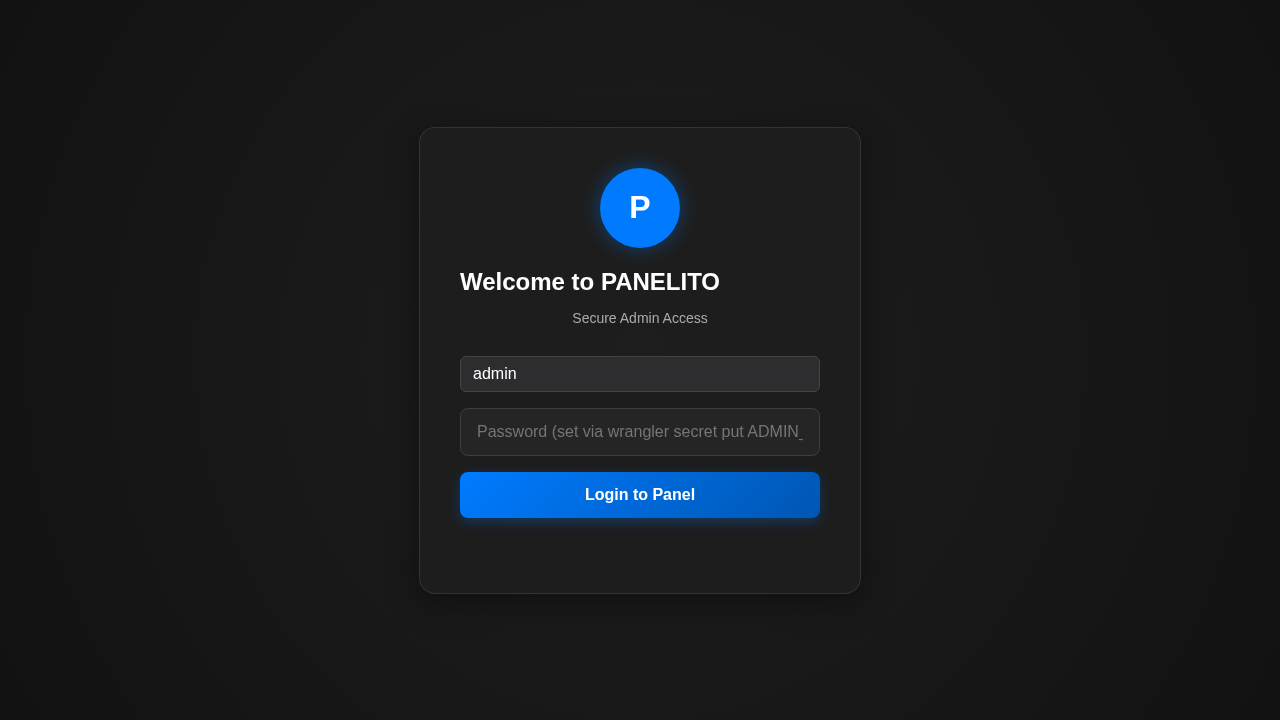
PANELITO
Credential Phishingtechnology | finance | ecommerce | cryptocurrency | other · 4/5/2026
This page at control.gamingvote.com presents a PANELITO Admin login UI, imitating an admin panel. The page title reads 'PANELITO Admin' and the static HTML shows a login section with a username default of 'admin' and a password field, while the domain is control.gamingvote.com which is a new domain (0 days old) under Cloudflare hosting. Network activity includes an off-domain endpoint and SPA-style credential capture potential via admin.js and a password field rendered in the SPA, indicating credential collection」という impersonation of an admin panel brand. The SSL certificate covers gamingvote.com and control.gamingvote.com, but the brand shown is PANELITO, not gamingvote, flagging brand impersonation and credential harvesting potential.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 1
Late-stage login UI: No
Resource Signals
Resources: 9
Hosts: 3
Domains: 3
Suspicious Endpoints
hxxps://usb[.]b63ccd22db3b4e5a4c4d[.]workers[.]dev/datasound/discord.mp3
Off-Domain Posts
hxxps://usb[.]b63ccd22db3b4e5a4c4d[.]workers[.]dev/datasound/discord.mp3
Scanner captured a new, unsigned admin panel mimic hosted at control.gamingvote.com. The page title and UI clearly imitate an unknown 'PANELITO' admin panel, while the domain is an unrelated, freshly registered subdomain under gamingvote branding. The static HTML contains a password field and a JavaScript bundle named admin.js, suggesting credential capture within a SPA. Off-domain exfiltration endpoints and beacon calls imply data collection and potential leakage. The combination of a brand-mismatch impersonation, a password input field, a 0-day domain, and suspicious external endpoints warrants immediate takedown action and suspension of the domain and hosting to prevent credential harvesting.
Suspend Domain