lemon.trueforceteam.ru
https://lemon.trueforceteam.ru/oyzy4kx8fjoz.html
91.92.243.119 · Omegatech LTD
New York, United States
—
200 · 59.6s
Valid· R12, Let's Encrypt, US
COMPLETED
Registered-domain escalation
Submit trueforceteam.ru as the primary IOC, enriched with evidence from hostile subdomains like lemon.trueforceteam.ru.
No KB/IOK detections were recorded for this scan.
AOL
Credential PhishingTechnology · 4/5/2026
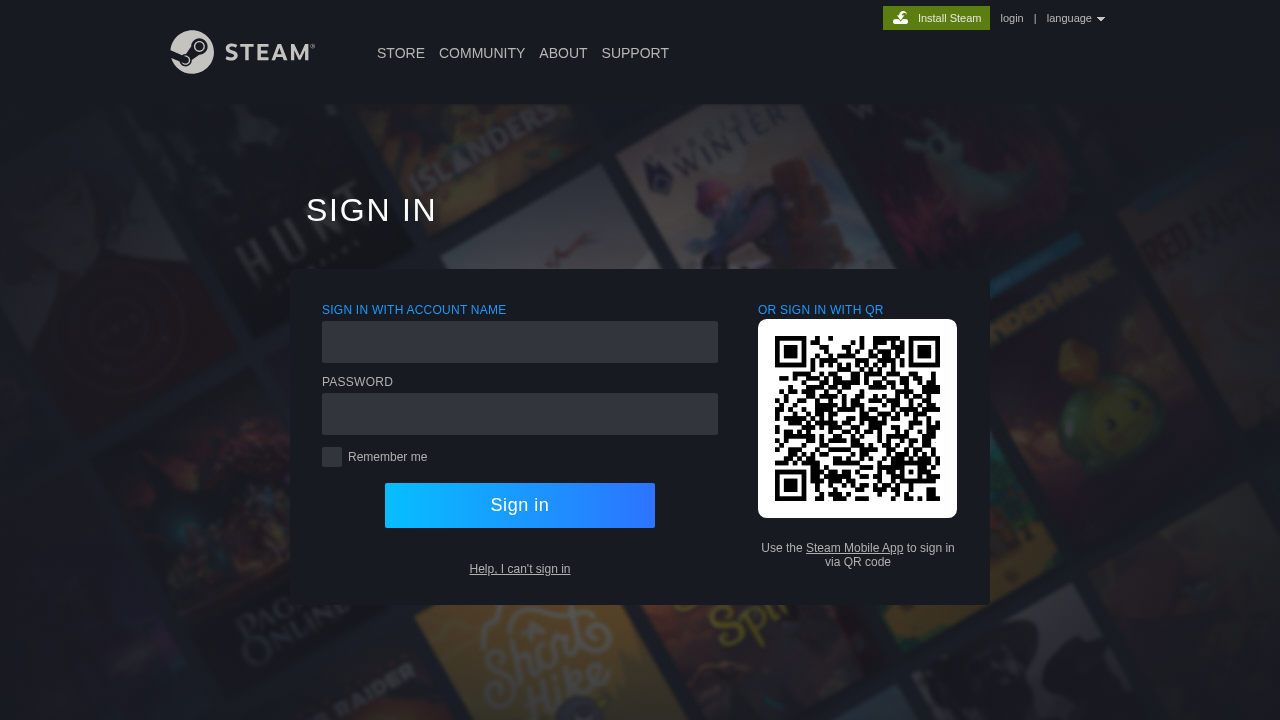
The page presents a Sign In interface that visually imitates AOL branding, but the domain lemon.trueforceteam.ru is not an official AOL domain. The UI shows a credential collection form rendered by JavaScript (SPA behavior) with a password field, and a suspicious off-domain POST target to https://easytrueforce.shop/... indicating credential exfiltration. The page title is Sign In and resources include a script pz4pp3b1jkpu.js loaded from the same domain, while an external POST endpoint on a different domain suggests credential theft flow. SSL is valid but issued recently; domain appears untrusted and the IP is registered to an unknown entity. Overall, evidence supports credential phishing via impersonation of AOL, delivered through a SPA login UI that collects credentials and transmits them to an attacker-controlled domain.
Capture
Stages: 2
Canonical: Settled Render
Changed: No
Credential Signals
Forms: 0
Password fields: 1
Late-stage login UI: No
Resource Signals
Resources: 6
Hosts: 2
Domains: 2
The scan shows strong phishing signals: the page imitates AOL branding on a non-official domain and dynamically renders a login form that captures credentials. The observed POST to an attacker-controlled domain indicates credential exfiltration. Although the SSL is valid, this is not enough to reassure; the domain’s branding and SPA behavior strongly suggest credential harvesting. Recommend treating as a credential-phishing campaign and taking action to block and investigate the domain and its hosting/redirect endpoints.
Suspend Domain