guileless-mooncake-6f836c.netlify.app
https://guileless-mooncake-6f836c.netlify.app/
18.208.88.157 · AWS EC2 (us-east-1)
Ashburn, United States
2865 days
200 · 27.6s
Valid· DigiCert Global G2 TLS RSA SHA256 2020 CA1, DigiCert Inc, US
COMPLETED
Registered-domain escalation
Submit netlify.app as the primary IOC, enriched with evidence from hostile subdomains like guileless-mooncake-6f836c.netlify.app.
No KB/IOK detections were recorded for this scan.
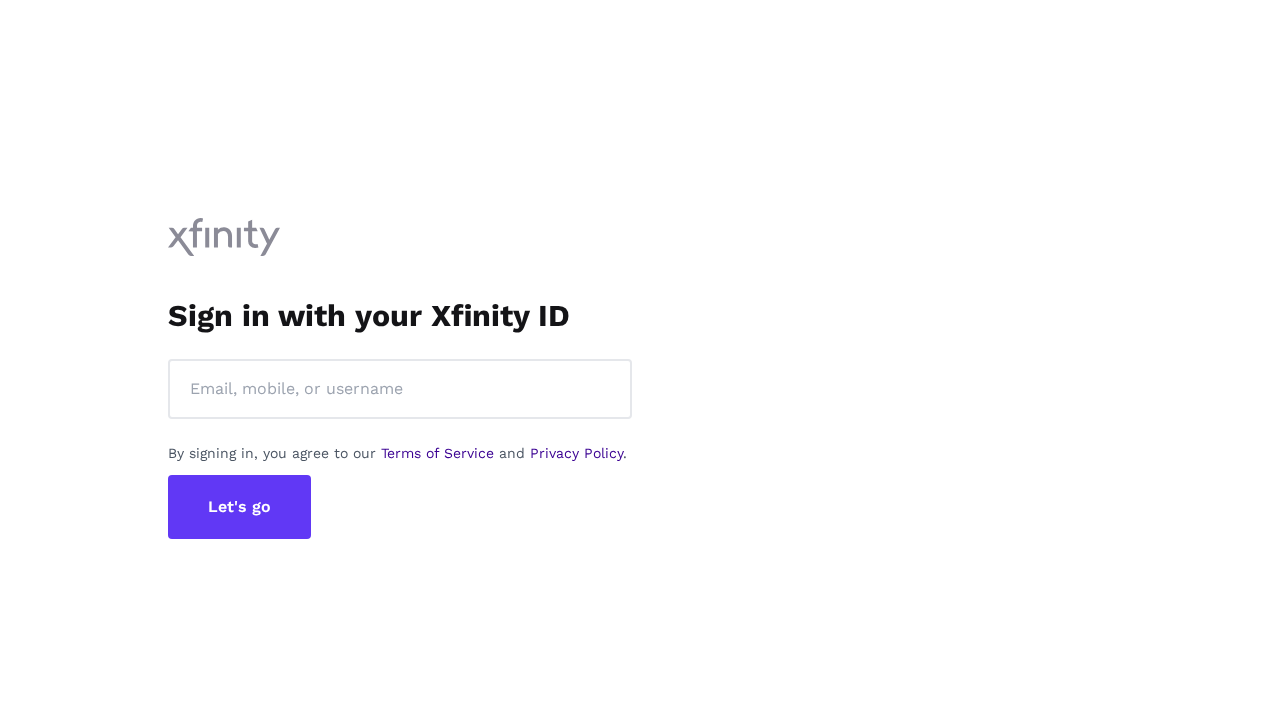
Xfinity
Credential Phishingfinance | technology | ecommerce | healthcare | government | social_media | cryptocurrency | telecommunications | education | other · 4/5/2026
This site at guileless-mooncake-6f836c.netlify.app is impersonating Xfinity by presenting a Sign in to Xfinity page. The page title and UI resemble Xfinity’s login flow, yet the domain is not an official Xfinity domain. The page loads a login form and collects credentials, indicating credential harvesting attempts.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 1
Password fields: 1
Late-stage login UI: No
Resource Signals
Resources: 11
Hosts: 6
Domains: 6
Suspicious Endpoints
hxxps://guileless-mooncake-6f836c[.]netlify[.]app/
hxxps://api[.]ipify[.]org/?format=json
hxxps://guileless-mooncake-6f836c[.]netlify[.]app/$%7BbaseURL%7Dmain
Off-Domain Posts
hxxps://api[.]ipify[.]org/?format=json
The page presents a credible credential phishing setup targeting Xfinity users. The non-official domain hosting a page with the exact branding and a password field constitutes impersonation and credential harvesting. The page includes a login form and uses external scripts/assets to render a Tailwind-based UI that mimics the legitimate service, and it contacts an off-domain endpoint (api.ipify.org) that could be used for exfiltration. Given the brand mismatch, the page poses a high risk to end users; immediate action to suspend domain and block hosting URL is recommended, with monitoring for related domains and screensharing of similar clones.
Monitor