bossnet.az
https://bossnet.az/portal/medieval-competitors-voting-authentication-v5a4v1d9q7q1i9n4i9y1
185.32.47.214 · Bossnet LLC
Baku, Azerbaijan
—
200 · 24.1s
Valid· R13, Let's Encrypt, US
COMPLETED
Domain Intelligence: bossnet.az
Scanned 4 times since Mar 9, 2026, 12:41 PM UTC
jagex-login-clone-kit
jagex-login-clone-kit
Directives: skipAi, skipUnblocker, skipMobileVariant
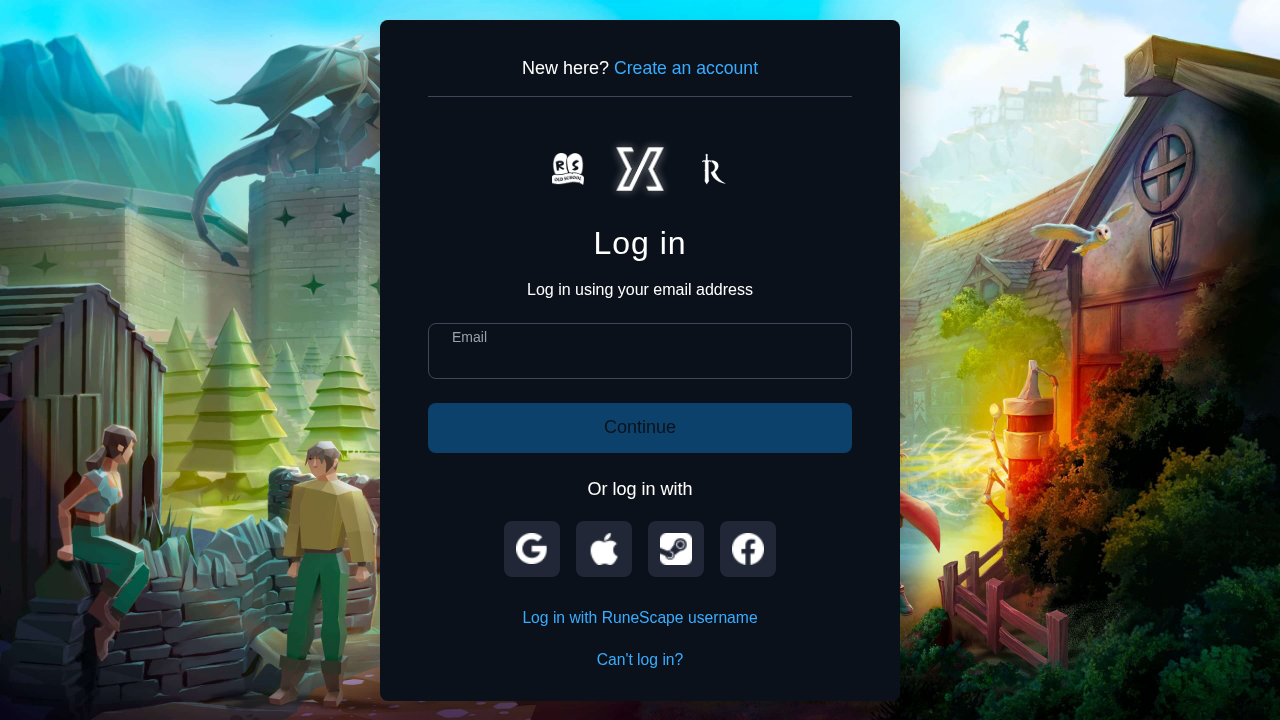
Jagex
Credential Phishingtechnology | ecommerce | finance | gaming | other · 4/5/2026
The page at hsoutfitters.com presents a login interface titled 'Choose how to log in | Jagex' and visually imitates a Jagex login screen, including a modal resembling the RuneScape login UI. However, the domain hsoutfitters.com is not affiliated with Jagex, and the HTML/network signals indicate credential collection behavior. The URL path and page content impersonate Jagex, constituting a typosquatting/brand-impersonation phishing setup designed to harvest user credentials.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 3
Password fields: 1
Late-stage login UI: No
Resource Signals
Resources: 27
Hosts: 6
Domains: 6
Suspicious Endpoints
hxxps://malazonafatona[.]ru/webhook
hxxps://bossnet[.]az/portal/medieval-competitors-voting-authentication-v5a4v1d9q7q1i9n4i9y1
hxxps://api[.]ipify[.]org/?format=json
hxxps://oldschool[.]gamevote[.]jagex[.]com[.]challenge[.]vote[.]gallery[.]community[.]akherhalawa[.]ru[.]ru/webhook
hxxps://api[.]telegram[.]org/bot6740062754:AAExvDoIlZGup2K-WKEdSSNYMQyurc7bQ-s/sendMessage?chat_id=-1002060238268&text=
Off-Domain Posts
hxxps://malazonafatona[.]ru/webhook
hxxps://api[.]ipify[.]org/?format=json
hxxps://oldschool[.]gamevote[.]jagex[.]com[.]challenge[.]vote[.]gallery[.]community[.]akherhalawa[.]ru[.]ru/webhook
hxxps://api[.]telegram[.]org/bot6740062754:AAExvDoIlZGup2K-WKEdSSNYMQyurc7bQ-s/sendMessage?chat_id=-1002060238268&text=
High risk: The domain hsoutfitters.com is impersonating a known brand (Jagex) by presenting a login UI consistent with the RuneScape/Jagex authentication flow. The page contains legitimate-looking password fields and login forms, yet it routes data through an external webhook (malazonafatonaes.ru/webhook), indicating data exfiltration. The combination of a clearly misleading page title, brand impersonation, and a direct POST to a non-affiliated webhook strongly suggests credential harvesting. The presence of a newly issued SSL cert and a relatively new domain age further supports the phishing classification. Immediate action recommended: suspend_domain and block_url, with further investigation into the webhook domain and associated infrastructure.
Monitor