prinvot.com
https://prinvot.com
82.221.129.24 · Icenetworks Ltd
Reykjavik, Iceland
6 days ⚠
200 · 15.2s
Valid· R13, Let's Encrypt, US
COMPLETED
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
Prinvot
Vendors
30/31
Status
partial
No KB/IOK detections were recorded for this scan.
Prinvot
Data Harvestingtechnology | ecommerce | finance · 4/5/2026
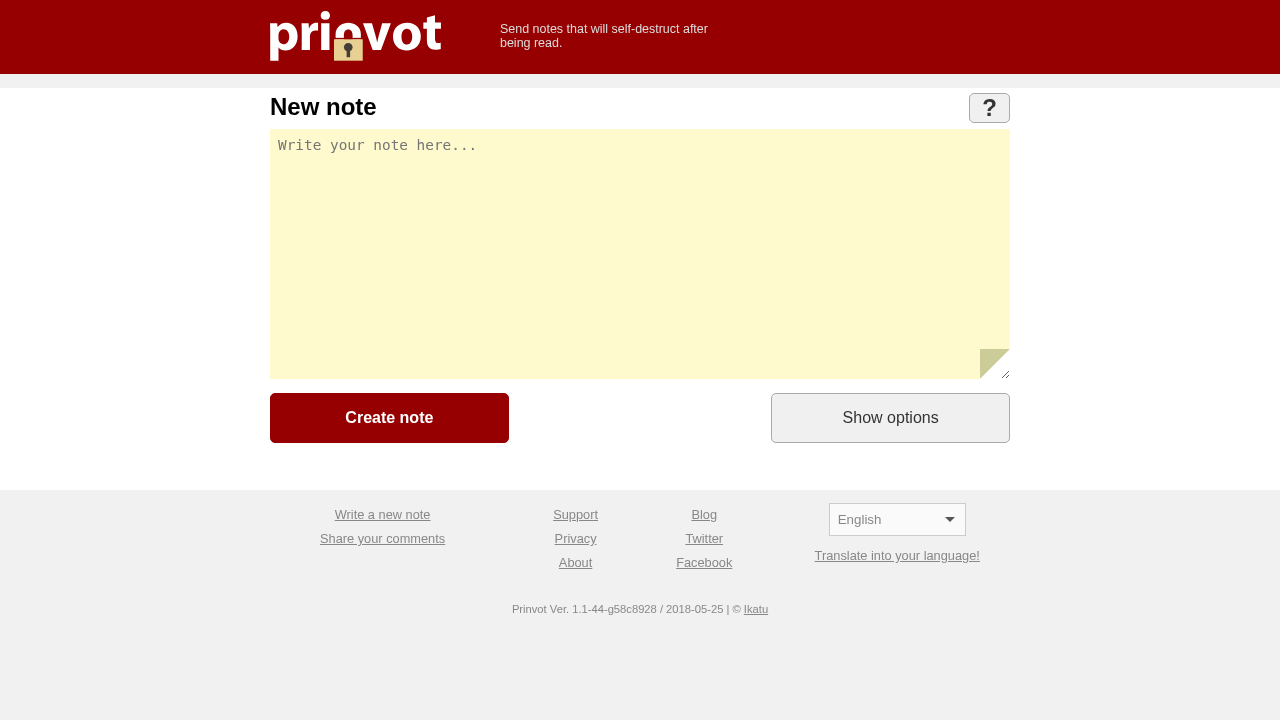
The page presents Prinvot branding and a note-destruct service, with a password field and an endpoint POST to /rum. Visuals show Prinvot branding (logo, title, colors) on the domain prinvot.com, which appears to be the official site. However, the site collects credentials via a password field and posts data to an internal endpoint, suggesting potential credential collection or exfiltration behavior. The domain is very new (6 days) with a Let's Encrypt cert and external scripts loaded, which may indicate a risk of misuse or rapid deployment. The combination of password input, suspicious POST endpoint, and non-standard external resources raises concerns about data harvesting rather than legitimate operation.
Capture
Stages: 2
Canonical: Settled Render
Changed: No
Credential Signals
Forms: 1
Password fields: 2
Late-stage login UI: No
Resource Signals
Resources: 25
Hosts: 3
Domains: 3
Suspicious Endpoints
hxxps://prinvot[.]com/
The domain prinvot.com is extremely new (6 days) and uses a password field with a POST request to /rum, which could indicate credential harvesting or data exfiltration in a credential-protected note service. The page uses external scripts from multiple third-party hosts, increasing risk of privacy leakage. While the branding and page title clearly identify Prinvot as a self-destructing notes service, the evidence of a password input UI and a POST endpoint for data collection elevates concern for credential or data harvesting abuse. Recommend monitoring and further domain intelligence checks; consider blocking or suspending if corroborated abuse signals persist.
Monitor