1kx.in
http://1kx.in/gB5PUp
13.204.27.94 · AWS EC2 (ap-south-1)
Mumbai, India
2817 days
200 · 53.7s
Valid· SSL.com RSA SSL subCA, SSL Corporation, US
COMPLETED
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
LuckySpy Casino
Vendors
28/30
Status
partial
No KB/IOK detections were recorded for this scan.
LuckySpy Casino
Unknowngambling · 4/29/2026
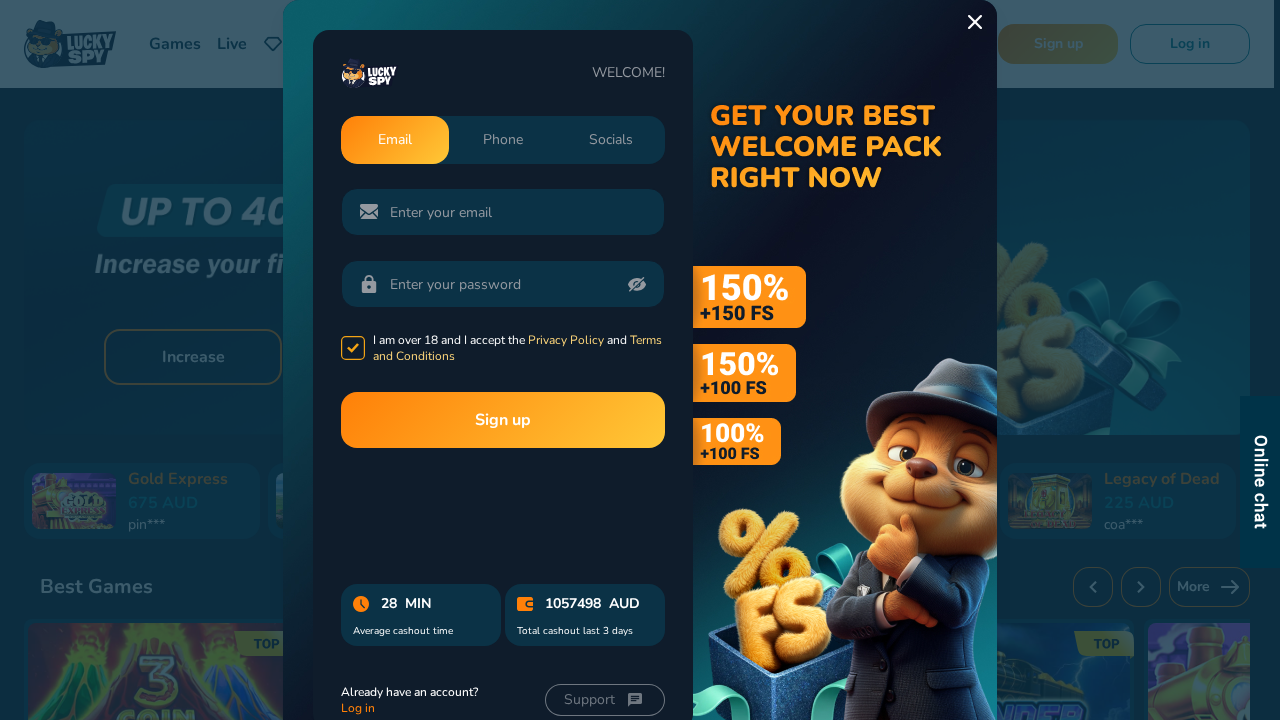
The scanned domain 1kx.in redirects to luckyspy.com which presents LuckySpy Casino branding. The page contains a login form and password field, but the visual evidence and URL paths indicate the site is a third-party gambling/affiliate/abuse platform rather than an official Lucky Spy casino domain. The domain 1kx.in is a typosquat-like domain that redirects to luckyspy.com, but the page itself appears to be LuckySpy’s own site rather than an impersonation of another brand. No clear credential harvesting or malware delivery found beyond typical login UI; however, the presence of a sign-up modal and tracking endpoints suggests potential data collection behavior consistent with an affiliate/chat widget integration.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 1
Password fields: 1
Late-stage login UI: No
Resource Signals
Resources: 170
Hosts: 10
Domains: 9
Suspicious Endpoints
hxxps://luckyspy[.]com/pre-chat/api/ask/get-setting
hxxps://luckyspy[.]com/en/sign-up
No suspicious indicators identified
The domain 1kx.in is a typosquatted gateway that redirects to luckyspy.com, which is a legitimate-looking LuckySpy Casino page with login UI and affiliate/tracking endpoints. This pattern is consistent with credential harvesting risk when a typosquat points to a brand’s landing page; combined with password field presence and sign-up modal, there is potential for user data collection if login actions are captured by LuckySpy’s scripts. However, the page ultimately appears to be a LuckySpy property rather than a seamless impersonation of a different brand. Recommend monitoring and verification of domain ownership and UX targeting; consider phishing risk due to typosquatting and potential credential collection via the sign-up/login surface.
Monitor