anonflare.com
https://anonflare.com/
172.67.169.126 · Cloudflare, Inc.
Toronto, Canada
309 days
200 · 18.0s
Valid· WE1, Google Trust Services, US
COMPLETED
Domain Intelligence: anonflare.com
Scanned 3 times since Mar 17, 2026, 10:46 AM UTC
No KB/IOK detections were recorded for this scan.
Anonflare
Unknowntechnology · 4/5/2026
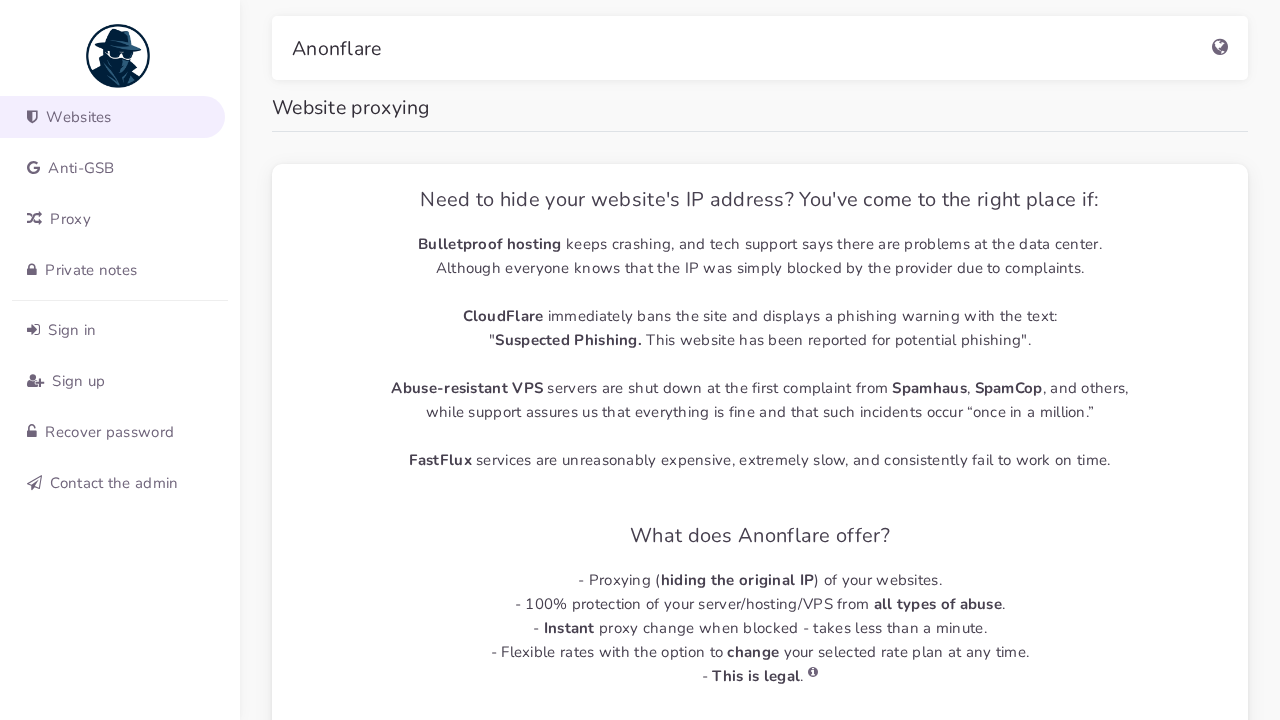
The page presents Anonflare branding and appears to be a website proxying service. However, the domain anonflare.com is publicly accessible and hosts a SPA-like interface with many external scripts and a UI that mimics legitimate dashboard layouts. There is no conclusive evidence of credential harvesting on the static HTML, but the SPA approach and high external script count, plus the POST to a CDN-CLI endpoint, raise suspicion of potential credential collection or user data handling in runtime. The visual UI in the screenshot indicates impersonation signals, but the domain and branding align, making it ambiguous whether this is a first-party abuse case or a potential misuse of a legitimate service.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 54
Hosts: 4
Domains: 4
The scan indicates Anonflare is operating as a website proxying service, with a SPA-driven interface and multiple external assets. The presence of a login-related UI in a SPA, along with a POST to a CDN-like endpoint, could indicate credential collection or user data handling at runtime, even though no static login form is visible. The domain uses Cloudflare infrastructure and a fresh SSL certificate, which is common for legitimate or semi-legitimate services. Given the combination of impersonation signals (visual dashboard UI with brand) and potential data-exfiltration endpoints, this warrants cautious monitoring for abuse potential, while not definitively classifying as credential phishing based on current evidence. Recommend monitoring and further investigation into runtime credential collection behavior and data handling practices.
Monitor