anonflare.cc
https://anonflare.cc/
104.21.79.77 · Cloudflare, Inc.
Toronto, Canada
2 days ⚠
200 · 27.7s
Valid· E8, Let's Encrypt, US
COMPLETED
Domain Intelligence: anonflare.cc
Scanned 2 times since Mar 20, 2026, 02:04 AM UTC
No KB/IOK detections were recorded for this scan.
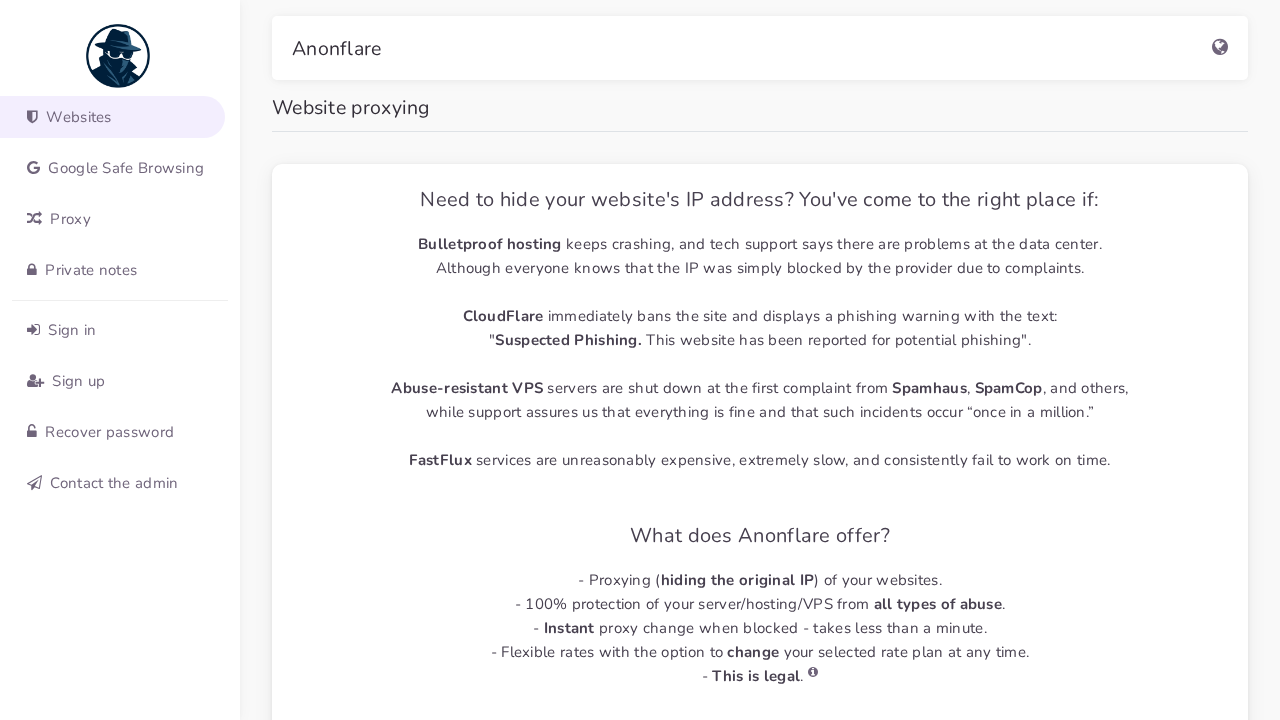
Anonflare
Unknowntechnology | ecommerce | finance | cryptocurrency | other · 4/5/2026
The site anonflare.cc presents as a website proxying service with a dashboard-like UI. The page title and UI text reference website proxying features, and the site is hosted behind Cloudflare. Visuals from the screenshot show an admin-like interface, but there is no recognizable consumer brand being impersonated. The domain is extremely new (2 days) and uses a free Let's Encrypt certificate; network activity includes multiple external JS/CSS assets and a POST to a CDN-rum endpoint, which may be used for telemetry or data exfiltration. The SPA nature suggests credential collection could be implemented client-side in scripts despite no static forms in HTML.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 54
Hosts: 4
Domains: 4
No specific IOCs identified in source
Highly suspicious; the domain anonflare.cc is extremely new (2 days) and is hosted behind Cloudflare with a free Let's Encrypt certificate, a pattern often seen in ephemeral phishing infrastructure. The site displays a dashboard-like UI under the brand Anonflare, but there is no explicit alignment with a known legitimate brand. The SPA architecture and large set of external scripts, plus a POST to a potential telemetry or data endpoint, strongly suggest credential or data harvesting capabilities embedded in the client-side code. Given the lack of an obvious legitimate branding and the aggressiveness of the setup, this domain should be treated as malicious and blocked. The presence of a 302/200 redirect chain and the explicit focus on proxy services amplify the risk of abuse and misdirection.
Monitor