bossnet.az
https://bossnet.az/portal/medieval-competitors-voting-authentication-v5a4v1d9q7q1i9n4i9y1
185.32.47.214 · Bossnet LLC
Baku, Azerbaijan
—
200 · 18.7s
Valid· R13, Let's Encrypt, US
COMPLETED
Domain Intelligence: bossnet.az
Scanned 4 times since Mar 9, 2026, 12:41 PM UTC
jagex-login-clone-kit
jagex-login-clone-kit
Directives: skipAi, skipUnblocker, skipMobileVariant
Jagex
Credential Phishingtechnology | gaming | ecommerce | finance | cryptocurrency · 4/5/2026
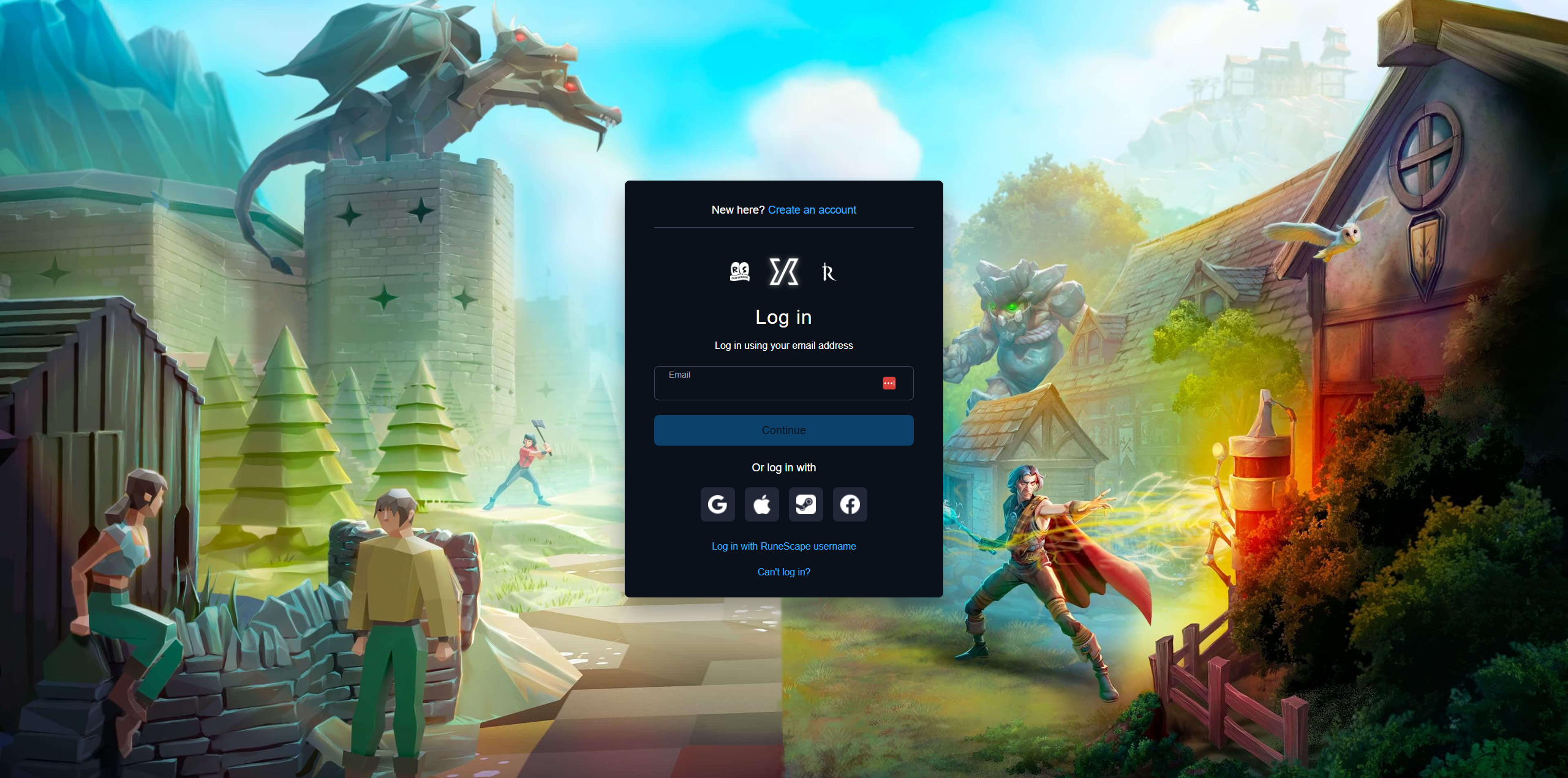
The page at bossnet.az presents a login screen styled similarly to Jagex, with a page title Choose how to log in | Jagex. Network activity includes a suspicious POST to malazonafatona.ru/webhook and several external assets under bossnet.az, but the page title and UI imitate a legitimate Jagex login, signaling impersonation. The domain bossnet.az is not the official Jagex domain, indicating brand spoofing and credential harvesting risk.
This site is actively attempting to harvest user credentials by presenting a login interface that imitates Jagex. The impersonation is supported by the page title and UI while the domain bossnet.az is not the official Jagex domain. The presence of a POST to an external webhook at malazonafatona.ru indicates data exfiltration to an unknown recipient, reinforcing malicious intent. The combination of a new, self-hosted domain with a valid SSL certificate and copied branding signals high risk of credential phishing; immediate action is warranted including domain suspension and hosting review. The scanner context notes that the page load bypassed cloaking and that a direct access attempt was made, corroborating live credential collection potential.
Monitor