tr.superbahis3.live
https://tr.superbahis3.live/
172.67.135.90 · Cloudflare, Inc.
Toronto, Canada
1 day ⚠
200 · 22.2s
Valid· WE1, Google Trust Services, US
COMPLETED
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
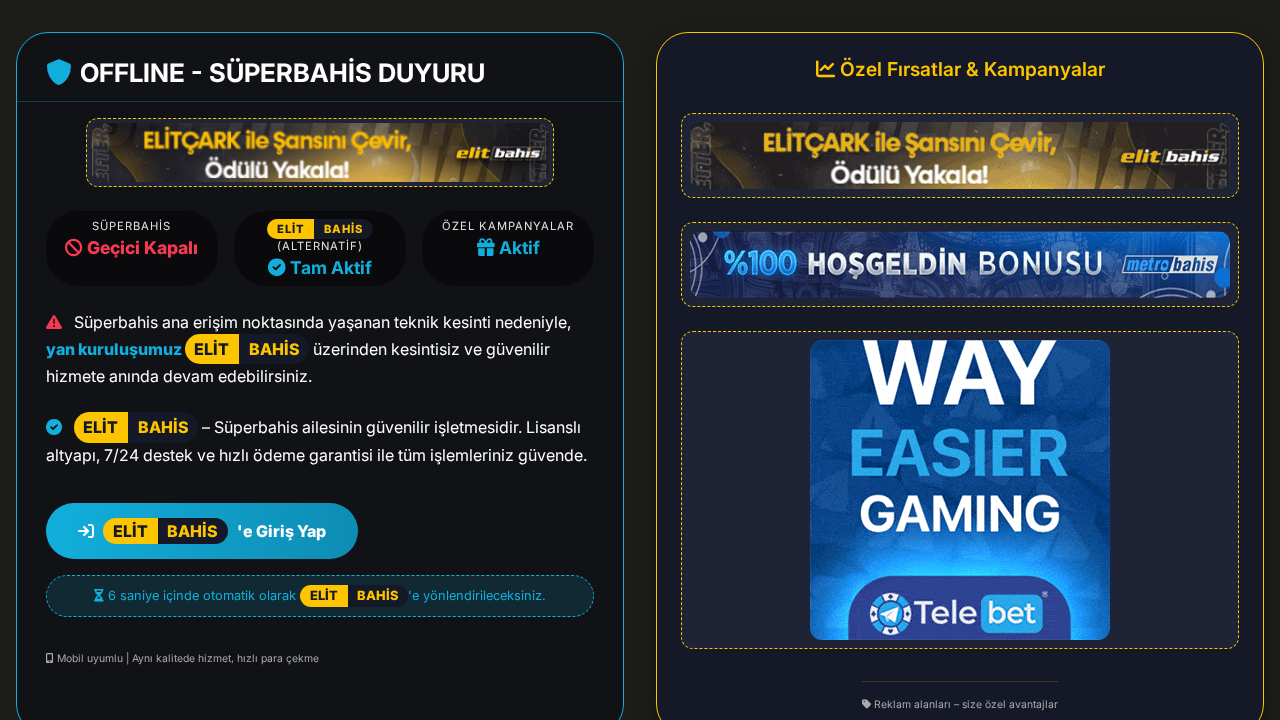
Elitbahis (presented as Süperbahis/Elitbahis combined branding)
Vendors
29/31
Status
partial
Registered-domain escalation
Submit superbahis3.live as the primary IOC, enriched with evidence from hostile subdomains like tr.superbahis3.live.
No KB/IOK detections were recorded for this scan.
Elitbahis (presented as Süperbahis/Elitbahis combined branding)
Unknowngambling | technology · 4/29/2026
The page is hosted at a new domain tr.superbahis3.live but redirects to venusmedya.net/superbahis.html. Visual branding imitates Elitbahis and Süperbahis styling, with Turkish text and embedded banners. However, the final URL differs from the initial domain, and the HTML shows a redirect/SPA-like setup with no static login form. The page appears to clone or impersonate betting brands, supported by the presence of deceptive redirect, off-brand hosting, and suspicious POST endpoints to cdn-cgi/rum? on external domains. There is no definitive credential harvesting form in static HTML, but dynamic credential capture could be present in the SPA JavaScript. Given the branding and suspicious redirect chain, this warrants attention for impersonation and potential credential phishing risk, though the evidence is not yet conclusive for active credential collection on the visible page.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 15
Hosts: 7
Domains: 7
The scan indicates strong impersonation signals: the visual branding aligns with Elitbahis, Süperbahis, and related campaigns, while the final URL is hosted on a different domain and redirects through multiple third-party hosts. The presence of off-domain POST endpoints and a SPA-like structure that could render credential collection scripts raises the risk of credential phishing or data harvesting. The combination of a very new domain, redirected final URL, and cross-domain exfiltration endpoints supports classifying this as suspicious/abusive, warranting containment actions and further verification with registrars and hosting providers. Monitor and consider domain and hosting takedown actions if corroborated by abuse teams.
Suspend Domain