cloud-user-base.com
https://cloud-user-base.com/iz5cw?utm_campaign=KV_726722336807197_0503_374_tsr_132&fbid=1231364054987195&utm_content=7sfx1en&cid=1_sales_701_ww_2460_m_fi&bid=BID&subid=2hf5i5.37b.13ios
172.67.187.165 · Cloudflare, Inc.
Toronto, Canada
5 days ⚠
200 · 19.5s
Valid· E7, Let's Encrypt, US
COMPLETED
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
Swyftx
Vendors
27/27
Status
completed
swyftx-clone-kit
swyftx-clone-kit
Directives: skipAi, skipUnblocker, skipMobileVariant
Swyftx
Unknowncryptocurrency | finance | technology | ecommerce · 6/3/2026
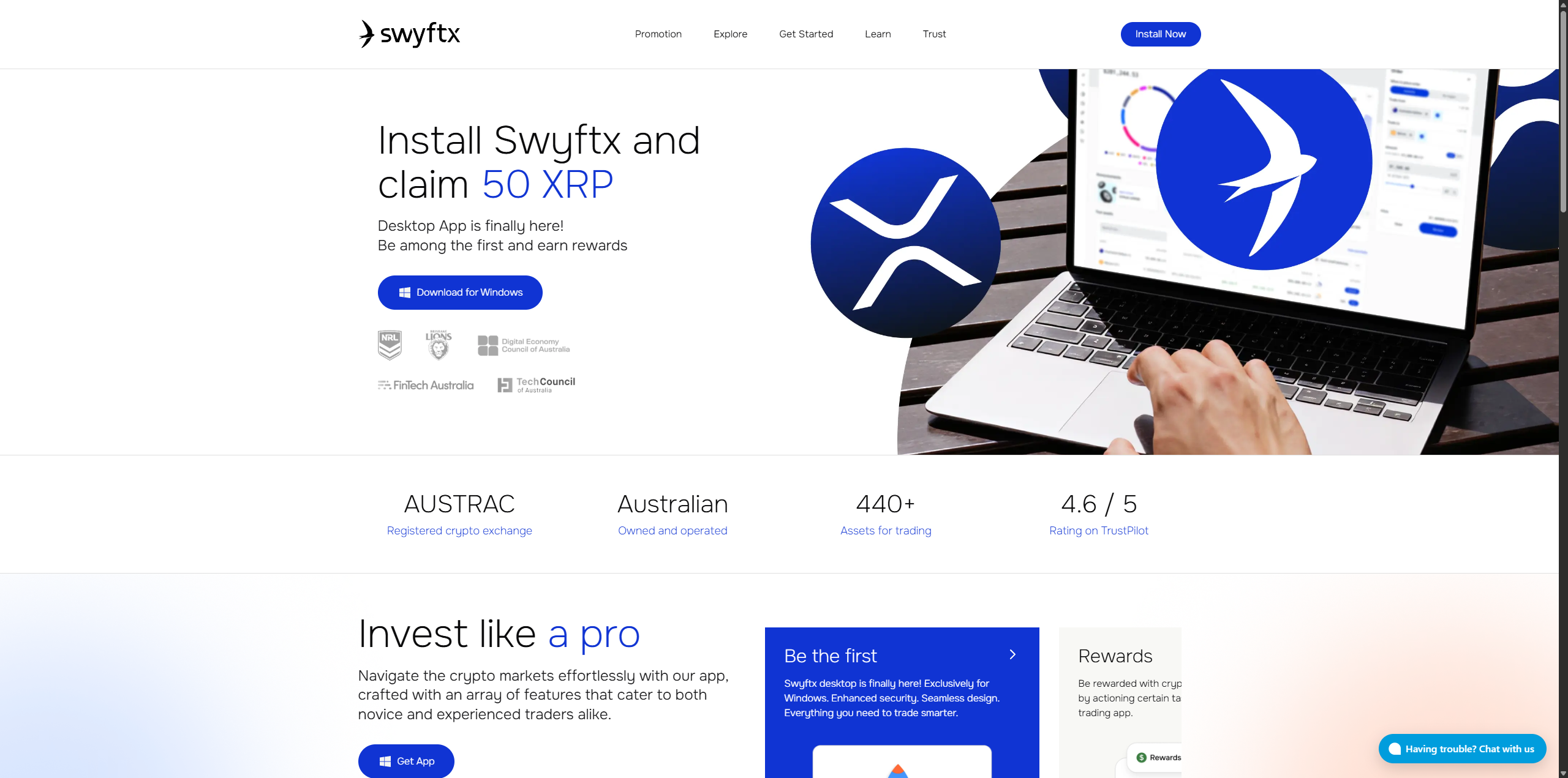
The page at cloud-user-base.com presents Swyftx branding and a Swyftx page title, but the domain is a new, non-official domain. The site loads Swyftx-like UI elements and assets, including a Swyftx page title, logo usage, and SPA-style asset loading, indicating impersonation designed to harvest credentials. This is a typosquat/brand impersonation attempt aimed at credential collection on a domain spoofing the legitimate Swyftx service.
This domain impersonates Swyftx, a recognized crypto exchange, using a newly registered domain and a page title that matches the brand. The HTML source shows an SPA structure with multiple external analytics scripts, and the page loads Swyftx-like branding and assets from cloud-user-base.com, which is not the legitimate Swyftx domain. The combination of brand impersonation, a very new domain, and embedded analytics promises data exfiltration via dynamically rendered forms. The presence of a blockable WAF or scanner-evasion indicators is not explicit, but the site actively loads tracking beacons and third-party scripts, increasing risk of credential harvesting. Recommend urgent takedown actions to prevent credential theft and brand abuse.
Monitor