tr.betboogir.live
https://tr.betboogir.live/
104.21.4.186 · Cloudflare, Inc.
Toronto, Canada
0 days ⚠
200 · 52.2s
Valid· WE1, Google Trust Services, US
COMPLETED
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
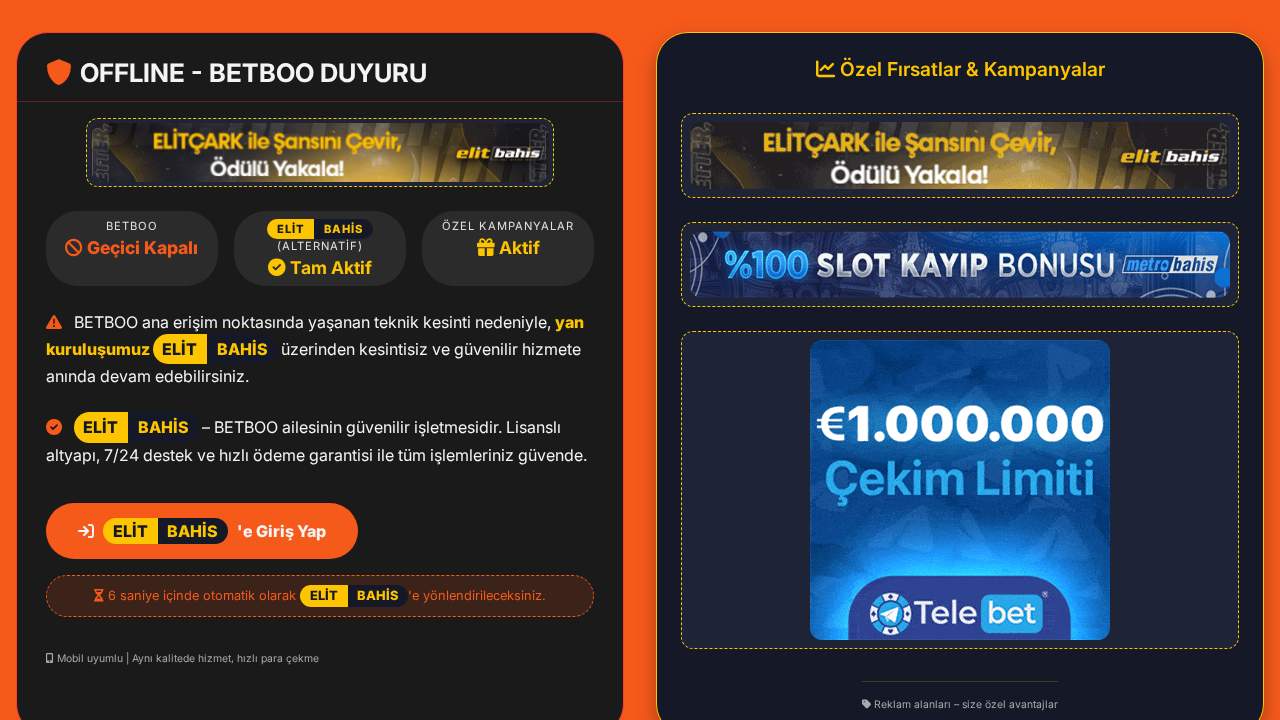
betboo (Elitbahis branding visible on page content)
Vendors
28/31
Status
partial
Registered-domain escalation
Submit betboogir.live as the primary IOC, enriched with evidence from hostile subdomains like tr.betboogir.live.
No KB/IOK detections were recorded for this scan.
Scanner blocked by cloudflare
This scan likely captured a block/challenge page, so the AI analysis may not reflect the real site victims see.
betboo (Elitbahis branding visible on page content)
Credential Phishingfinance | technology | ecommerce | gambling | social_media | cryptocurrency | telecommunications | education | other · 4/29/2026
The page presents BETBOO/Elitbahis branding and a Turkish UI motif but is hosted on a newly registered, non-official domain (tr.betboogir.live) that redirects to getverified3.top/betboo.html. The final URL and embedded assets indicate imitation of a known betting brand (Elitbahis/Betboo) with an SPA-like structure that may render credential forms via JavaScript. The presence of dynamic credential capture indicators (POSTs to a challenge platform URL, multiple external script/assets, and an iframe-like setup) supports potential credential harvesting rather than legitimate first-party content. The overall setup, including new domain age, rapid redirect chain, and off-brand hosting, strongly suggests impersonation/phishing activity rather than a benign first-party page.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 18
Hosts: 7
Domains: 7
The domain tr.betboogir.live is extremely new (0 days old) and resolves through a redirect chain to a separate domain getverified3.top that hosts a poker-like Betboo/Elitbahis styled page. The page HTML indicates an SPA structure without static forms, suggesting credential capture via dynamically loaded UI. The presence of suspicious POST targets and off-domain exfiltration endpoints, combined with a WAF-block context, strongly indicates an attempted phishing or credential harvesting operation. Given the branding mimicry and redirect flow, this is high-risk for user credential theft. Monitor and consider blocking suspension actions.
Suspend Domain