detuks-client.com
https://detuks-client.com/
172.67.138.101 · Cloudflare, Inc.
Toronto, Canada
103 days
200 · 28.5s
Valid· WE1, Google Trust Services, US
COMPLETED
Linked Phishing Report
This scan is attached to a vendor submission report
Brand
Detuks Client
Vendors
30/30
Status
completed
No KB/IOK detections were recorded for this scan.
Detuks Client
Data Harvestingtechnology | ecommerce · 6/3/2026
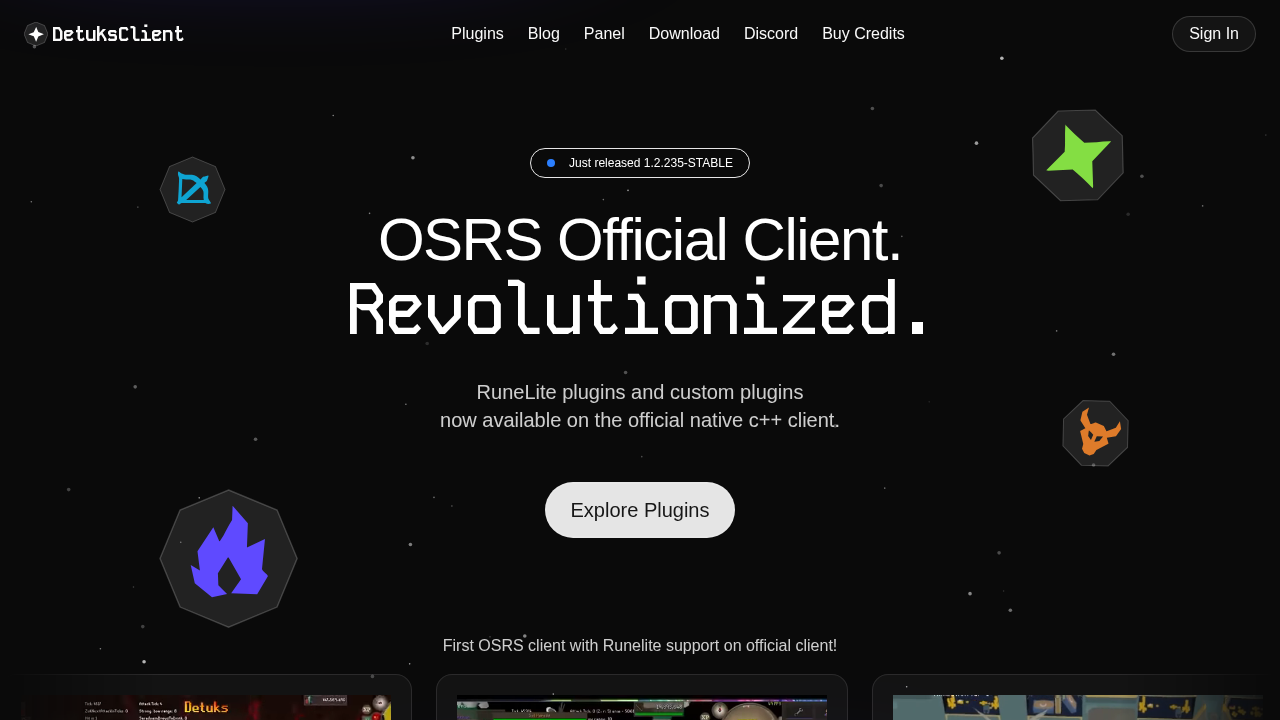
The page presents as Detuks Client, a RuneLite-based OSRS plugin store/client. However, the static HTML contains no forms, and the SPA is heavy with external JS bundles. Visual cues and the screenshot indicate a consumer-facing product site rather than a classic credential-phishing page, but the SPA rendering means credential capture could occur in the executed JavaScript. The domain age is moderate (103 days) with a recent certificate. There is no explicit impersonation of a well-known brand in the visible branding, but the page’s structure and numerous external scripts warrant caution for credential collection via dynamic UI.
Capture
Stages: 3
Canonical: Late Render (+3s)
Changed: No
Credential Signals
Forms: 0
Password fields: 0
Late-stage login UI: No
Resource Signals
Resources: 77
Hosts: 5
Domains: 3
Suspicious Endpoints
hxxps://detuks-client[.]com/api/auth/get-session
hxxps://detuks-client[.]com/api/trpc/user.get?batch=1&input=%7B%220%22%3A%7B%22json%22%3Anull%2C%22meta%22%3A%7B%22values%22%3A%5B%22undefined%22%5D%2C%22v%22%3A1%7D%7D%7D
The site is a live SPA-based product site for Detuks Client with OSRS plugins. There is no clear credential-harvesting form visible in static HTML, but the SPA architecture means credential capture could be performed by dynamically loaded JavaScript. The scanner detected 62 external scripts and several network requests, including an analytics endpoint, which can be normal for a storefront but also provides an avenue for hidden analytics or data exfiltration if misused. Given the lack of static forms and the branding aligned with the Detuks brand, there is not strong evidence of impersonation of a third-party brand, but the dynamic rendering and WAF-related network activity warrant cautious monitoring for potential credential collection via the SPA.
Monitor