www.facebook.com
https://www.facebook.com/profile.php?id=61582825777350
57.145.2.1 · Meta Platforms Ireland Limited
Ashburn, United States
10608 days
200 · 20.1s
Valid· DigiCert Global G2 TLS RSA SHA256 2020 CA1, DigiCert Inc, US
COMPLETED
Domain Intelligence: facebook.com
Scanned 5 times since Feb 17, 2026, 09:40 AM UTC
Registered-domain escalation
Submit facebook.com as the primary IOC, enriched with evidence from hostile subdomains like www.facebook.com.
No KB/IOK detections were recorded for this scan.
Technology · 4/29/2026
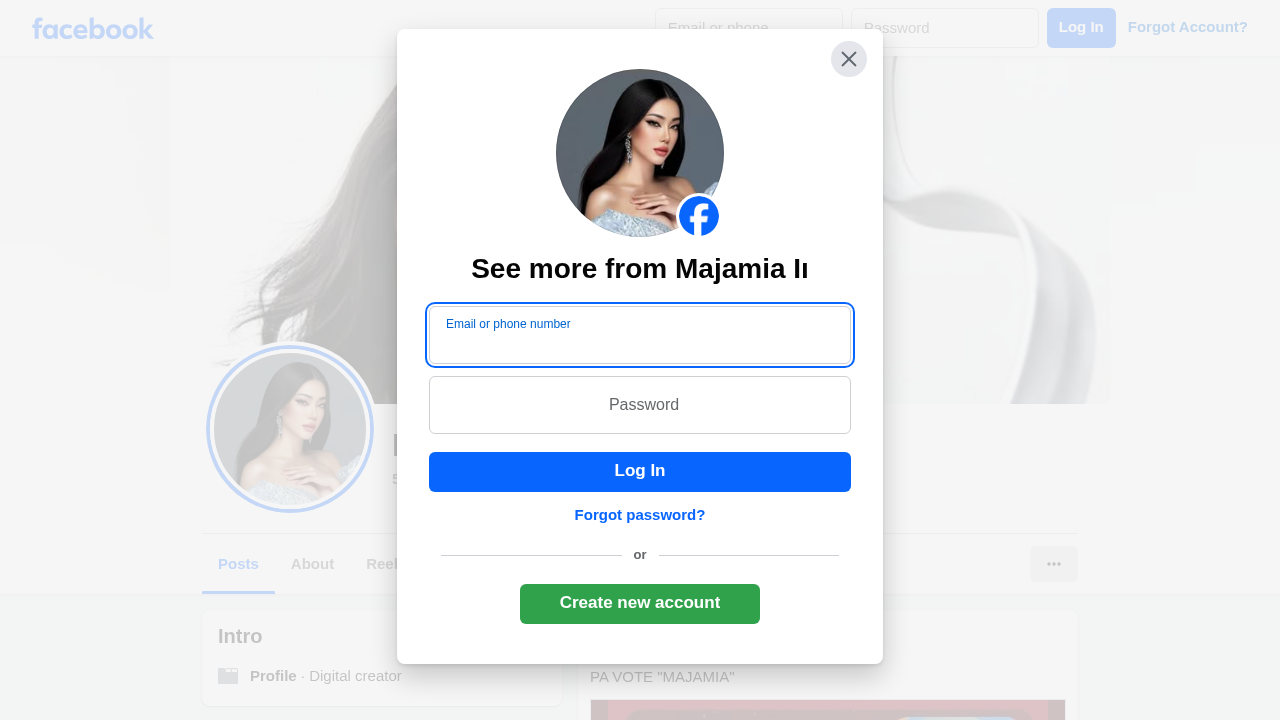
The page presents Facebook branding and content but is loaded from a profile path on the official facebook.com domain, with a suspicious modal overlay that resembles a login/credential capture UI. Evidence includes a visible login form in the static HTML, password field, and multiple authentication-related POST endpoints observed to the Facebook AJAX API, which, combined with the screenshot showing a login modal over a profile page, strongly suggests credential collection attempts disguised as a profile view. However, the domain and canonical page URL align with Facebook’s real service, so the page is more correctly categorized as first-party with potential abuse signals rather than a blatant impersonation of an external brand.
Capture
Stages: 2
Canonical: Settled Render
Changed: No
Credential Signals
Forms: 2
Password fields: 2
Late-stage login UI: No
Resource Signals
Resources: 116
Hosts: 7
Domains: 2
Suspicious Endpoints
hxxps://www[.]facebook[.]com/login/device-based/regular/login/?login_attempt=1
No specific IOCs identified in source
The scan shows legitimate Facebook branding and page structure with a prominent login modal overlay containing a password field and credential-collection form. While these signals could indicate a credential-phishing attempt, the domain is the official Facebook domain, which reduces impersonation risk. Nonetheless, the presence of a login form and multiple credential-related network calls on a user profile page could be used abusively to harvest credentials if presented in an deceptive context. Recommend monitoring for unusual or deceptive UI overlays that imitate Facebook login outside of canonical login flows, and flag for review if the page is being served in an unusual context or via a redirect path commonly used by phishing campaigns.
Monitor