www.facebook.com
https://www.facebook.com/profile.php?id=61585918043299
57.145.2.1 · Meta Platforms Ireland Limited
Ashburn, United States
10612 days
200 · 19.9s
Valid· DigiCert Global G2 TLS RSA SHA256 2020 CA1, DigiCert Inc, US
COMPLETED
Domain Intelligence: facebook.com
Scanned 5 times since Feb 17, 2026, 09:40 AM UTC
Registered-domain escalation
Submit facebook.com as the primary IOC, enriched with evidence from hostile subdomains like www.facebook.com.
No KB/IOK detections were recorded for this scan.
Technology · 4/29/2026
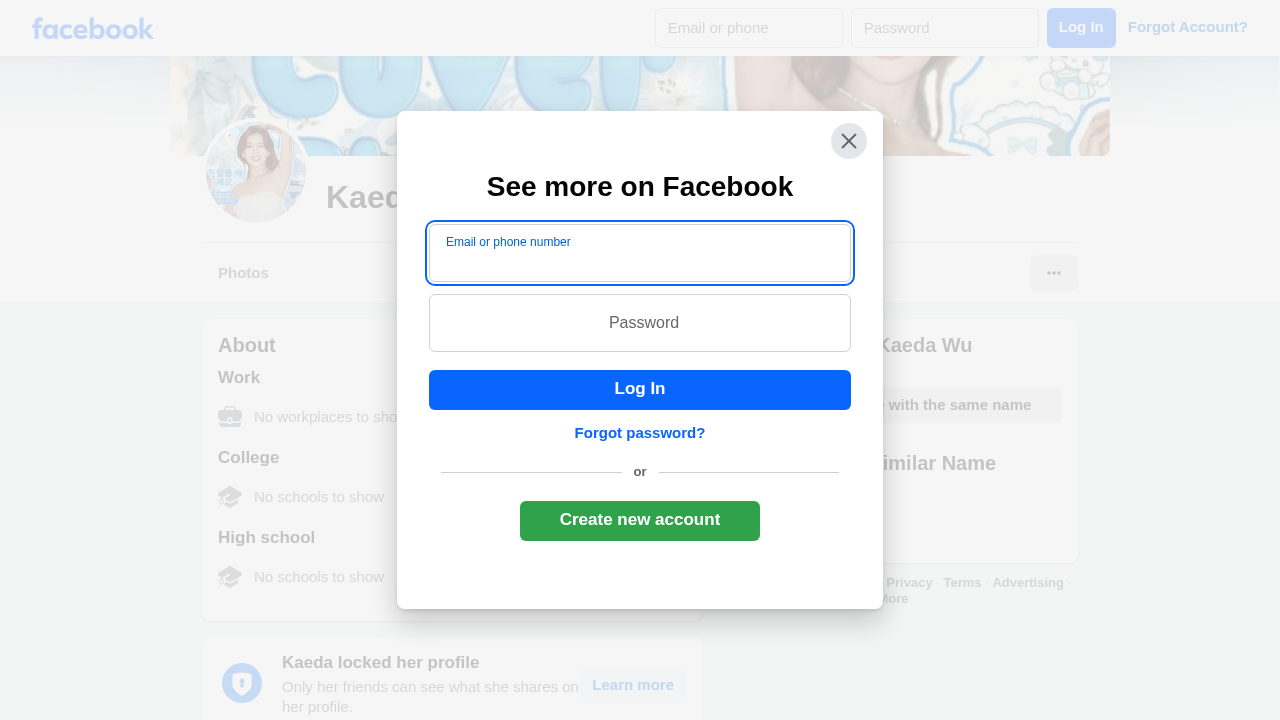
The page presents Facebook branding and a login UI overlaid by a modal that mimics Facebook's login prompt. However, the URL and page context show an actual Facebook profile path under www.facebook.com, suggesting this could be a first-party page. The screenshot reveals a prominent login dialog titled See more on Facebook with email/phone and password fields, which resembles a credential-collecting surface. Given the strong impersonation signals in the UI and the presence of login fields, this could be used for credential harvesting if hosted on a non-official Facebook page; combined with observed network/activity, it warrants careful verification of first/third-party status. Analyst flagged likely cloaking/evasion behavior for this target. Analyst context noted: Analyst note: this target may cloak content or block scanners.
Capture
Stages: 2
Canonical: Settled Render
Changed: No
Credential Signals
Forms: 2
Password fields: 2
Late-stage login UI: No
Resource Signals
Resources: 64
Hosts: 5
Domains: 2
Suspicious Endpoints
hxxps://www[.]facebook[.]com/login/device-based/regular/login/?login_attempt=1
The page shows concrete login UI elements and credential fields that resemble a legitimate Facebook login prompt, which is a common tactic for credential harvesting. While the hostname www.facebook.com and the page content correlate with Facebook branding, the analyst notes indicate possible cloaking and impersonation risk. The presence of a prominent 'See more on Facebook' modal with email/phone and password fields, along with POST login endpoints, supports potential credential collection behavior. Given the combination of impersonation signals and the possibility of this being a first-party page, this requires confirmation of brand integrity and monitoring for anomalous redirects or form handling. Recommend monitoring and verify domain/source alignment before taking action. Analyst-reported cloaking/evasion suspicion increases confidence that the operator is actively attempting to evade automated security analysis. Analyst context was provided and corroborated during this assessment (Analyst note: this target may cloak content or block scanners.).
Monitor